The Iranian-origin menace actor referred to as Charming Kitten has been linked to a brand new set of assaults geared toward Center East coverage consultants with a brand new backdoor known as BASICSTAR by making a faux webinar portal.
Charming Kitten, additionally known as APT35, CharmingCypress, Mint Sandstorm, TA453, and Yellow Garuda, has a historical past of orchestrating a variety of social engineering campaigns that forged a large internet of their focusing on, typically singling out assume tanks, NGOs, and journalists.
“CharmingCypress typically employs uncommon social-engineering ways, resembling participating targets in extended conversations over electronic mail earlier than sending hyperlinks to malicious content material,” Volexity researchers Ankur Saini, Callum Roxan, Charlie Gardner, and Damien Money mentioned.
Final month, Microsoft revealed that high-profile people engaged on Center Jap affairs have been focused by the adversary to deploy malware resembling MischiefTut and MediaPl (aka EYEGLASS) which can be able to harvesting delicate data from a compromised host.
The group, assessed to be affiliated with Iran’s Islamic Revolutionary Guard Corps (IRGC), has additionally distributed a number of different backdoors resembling PowerLess, BellaCiao, POWERSTAR (aka GorjolEcho), and NokNok over the previous yr, emphasizing its willpower to proceed its cyber onslaught, adapting its ways and strategies regardless of public publicity.
The phishing assaults noticed between September and October 2023 concerned the Charming Kitten operators posing because the Rasanah Worldwide Institute for Iranian Research (IIIS) to provoke and construct belief with targets.
The phishing makes an attempt are additionally characterised by means of compromised electronic mail accounts belonging to respectable contacts and a number of threat-actor-controlled electronic mail accounts, the latter of which is known as Multi-Persona Impersonation (MPI).
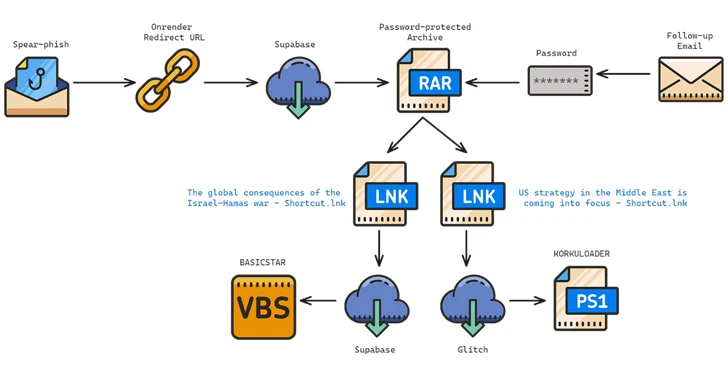
The assault chains usually make use of RAR archives containing LNK recordsdata as a place to begin to distribute malware, with the messages urging potential targets to affix a faux webinar about matters which can be of curiosity to them. One such multi-stage an infection sequence has been noticed to deploy BASICSTAR and KORKULOADER, a PowerShell downloader script.
BASICSTAR, a Visible Primary Script (VBS) malware, is able to gathering primary system data, remotely executing instructions relayed from a command-and-control (C2) server, and downloading and displaying a decoy PDF file.
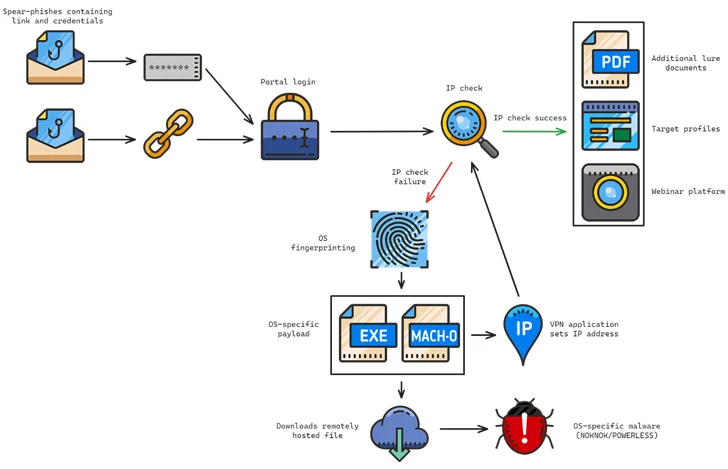
What’s extra, a few of these phishing assaults are engineered to serve totally different backdoors relying on the machine’s working system. Whereas Home windows victims are compromised with POWERLESS, Apple macOS victims are focused with an an infection chain culminating in NokNok through a useful VPN utility that is laced with malware.
“This menace actor is very dedicated to conducting surveillance on their targets with a view to decide how finest to govern them and deploy malware,” the researchers mentioned. “Moreover, few different menace actors have constantly churned out as many campaigns as CharmingCypress, dedicating human operators to assist their ongoing efforts.”
The disclosure comes as Recorded Future uncovered IRGC’s focusing on of Western nations utilizing a community of contracting corporations that additionally specialise in exporting applied sciences for surveillance and offensive functions to nations like Iraq, Syria, and Lebanon.
The connection between intelligence and navy organizations and Iran-based contractors takes the type of numerous cyber facilities that act as “firewalls” to hide the sponsoring entity.
They embody Ayandeh Sazan Sepher Aria (suspected to be related to Emennet Pasargad), DSP Analysis Institute, Sabrin Kish, Soroush Saman, Mahak Rayan Afraz, and the Parnian Telecommunication and Digital Firm.
“Iranian contracting corporations are established and run by a tight-knit community of personas, who, in some circumstances, signify the contractors as board members,” the corporate mentioned. “The people are intently related to the IRGC, and in some circumstances, are even representatives of sanctioned entities (such because the IRGC Cooperative Basis).”