Microsoft on Tuesday launched patches for 33 vulnerabilities, together with 24 for Home windows. 5 different product teams are additionally affected. Of the CVEs addressed, simply 4 are thought of Vital in severity – not less than by Microsoft. (Extra on that in a second.) Three of Microsoft’s Vital-severity patches have an effect on Home windows, whereas the opposite one impacts each Azure and Microsoft Energy Platform Connector. (Connectors are proxies or wrappers round APIs that enable the underlying companies to attach to one another; Microsoft has a really giant ecosystem of those integration instruments.)
At patch time, not one of the points are recognized to be underneath exploit within the wild, and none have been publicly disclosed. Nevertheless, absolutely a 3rd of the addressed vulnerabilities in Home windows and Defender – 11 CVEs — are by the corporate’s estimation extra more likely to be exploited within the subsequent 30 days.
Along with these CVEs, Microsoft lists one official advisory, ADV990001, which covers their newest servicing stack updates. Nevertheless, Edge-related points, which aren’t tallied within the official rely, make a robust displaying this month with 9 CVEs. Seven of these, together with 5 coming to Edge by means of the Chromium undertaking, had been launched on December 7. Of the opposite two launched at present, one elevation-of-privilege vulnerability (CVE-2023-35618) has the peculiar high quality of being a mere moderate-severity challenge in Microsoft’s estimation, however value a critical-class 9.6 CVSS base rating. The problem requires a sandbox escape to perform, and Microsoft assesses it as much less more likely to be exploited inside the subsequent 30 days, however we do advocate conserving Edge and different Chromium-based browsers updated.
We don’t embody Edge points within the CVE counts and graphics under, however we’ll present info on all the pieces in an appendix on the finish of the article. We’re as typical together with on the finish of this publish three different appendices itemizing all Microsoft’s patches, sorted by severity, by predicted exploitability, and by product household.
By the numbers
- Complete Microsoft CVEs: 33
- Complete Microsoft advisories delivery in replace: 1
- Complete Edge / Chromium points coated in replace: 9
- Publicly disclosed: 0
- Exploited: 0
-
- Severity:
- Vital: 4
- Necessary: 29
-
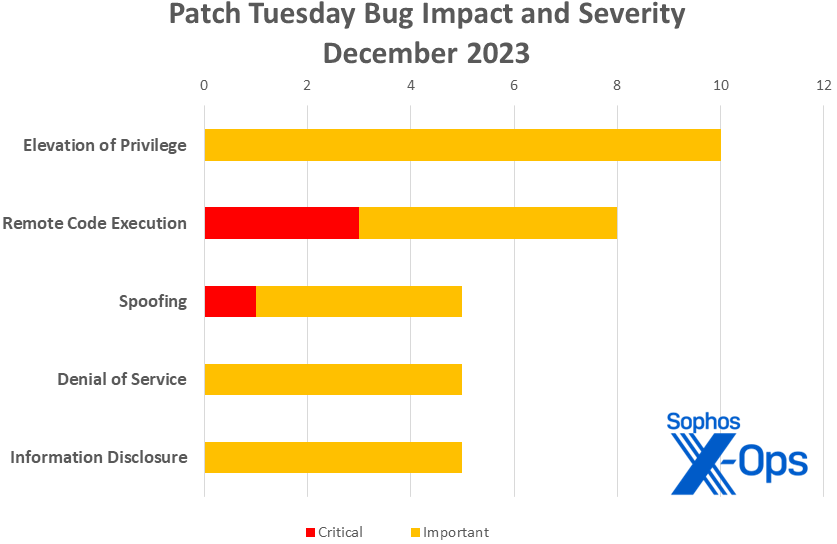
- Impression:
- Elevation of Privilege: 10
- Distant Code Execution: 8
- Denial of Service: 5
- Data Disclosure: 5
- Spoofing: 5
Determine 1: One thing you don’t see each month: A Vital-class spoofing bug
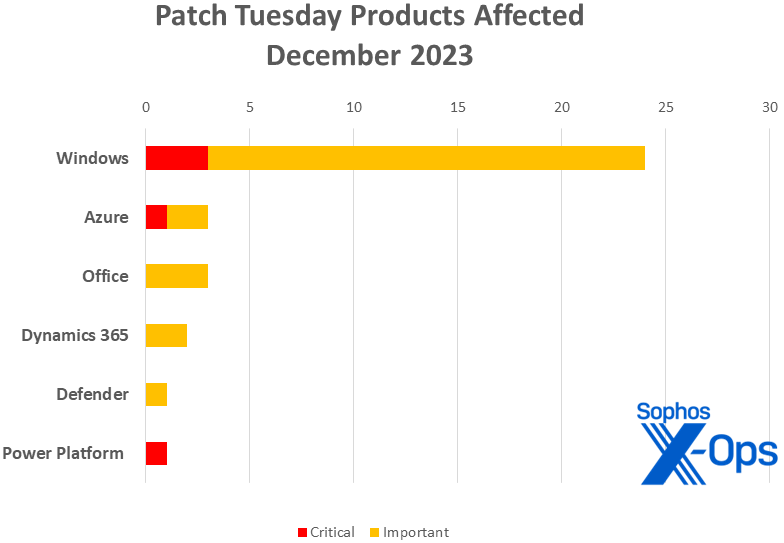
Merchandise
- Home windows: 24
- Workplace: 3
- Azure: 3 (together with one shared with Energy Platform)
- Dynamics 365: 2
- Defender: 1
- Energy Platform: 1 (shared with Azure)
Determine 2: As typical, Home windows CVEs are the majority of the gathering in December. The Vital-class vulnerability seen in each Azure and Energy Platform is similar CVE, affecting each product households
Notable December updates
Along with the problems mentioned above, just a few attention-grabbing objects current themselves.
CVE-2023-36019 — Microsoft Energy Platform Connector Spoofing Vulnerability
A Vital-severity spoofing challenge? Sure, and one in want of your immediate consideration – for those who haven’t already given it that. Connectors are essential behind-the-scenes performance for each Energy Platform and Azure, and this challenge is important sufficient that Microsoft has already notified affected clients about needed protecting actions beginning final month. (If this doesn’t ring a bell, you may not have a worldwide administrator function or a Message middle privateness reader function; for Logic Apps buyer, a notification was despatched by way of Service Well being within the Azure Portal underneath monitoring ID 3_SH-LTG.) To use this, an attacker would ship a malicious hyperlink, or they may manipulate a hyperlink, file, or software to disguise it as a reliable and reliable one. Microsoft has additionally revealed additional info on mitigations and upcoming modifications to authentication for buyer connectors.
CVE-2023-35628 — Home windows MSHTML Platform Distant Code Execution Vulnerability
The unhealthy information is that this Vital-severity RCE might in some eventualities result in a drive-by exploit, executing on the sufferer’s machine earlier than the sufferer even views a malicious e mail in Preview Pane, not to mention truly opens it. The excellent news is that based on Microsoft, this vulnerability depends on some advanced memory-shaping strategies to work. That mentioned, it impacts each client- and server-side working methods from Home windows 10 and Home windows Server 2012 R2 ahead, and Microsoft believes it’s one of many 11 extra more likely to be exploited inside the subsequent 30 days. Greatest to not delay.
CVE-2023-35619 — Microsoft Outlook for Mac Spoofing Vulnerability
CVE-2023-36009 — Microsoft Phrase Data Disclosure Vulnerability
Pleased holidays, Apple people! Microsoft Workplace LTSC for Mac 2021 takes two Necessary-severity patches this month.
CVE-2023-35638 — DHCP Server Service Denial of Service Vulnerability
CVE-2023-35643 — DHCP Server Service Data Disclosure Vulnerability
CVE-2023-36012 — DHCP Server Service Data Disclosure Vulnerability
The 30-year-old Dynamic Host Configuration Protocol takes three Necessary-severity patches this month, none of which cowl the DHCP-centric PoolParty process-injection approach demonstrated at this month’s BlackHat EU.
System directors are reminded that it’s nonetheless, total, a gradual month after a busy yr of Alternate patches. If attainable, this can be a good time to compensate for your Alternate patch state of affairs earlier than the 2024 cycle begins.
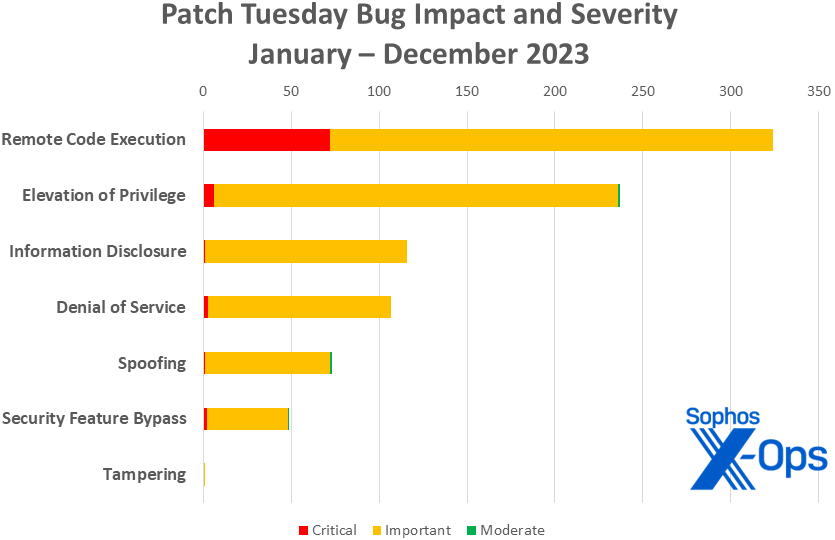
Determine 3: And because the yr rolls to a detailed, distant code execution points cement their place on the high of the 2023 charts
Sophos protections
| CVE | Sophos Intercept X/Endpoint IPS | Sophos XGS Firewall |
| CVE-2023-35631 | Exp/2335631-A | Exp/2335631-A |
| CVE-2023-35632 | Exp/2335632-A | Exp/2335632-A |
| CVE-2023-35644 | Exp/2335644-A | Exp/2335644-A |
| CVE-2023-36005 | Exp/2336005-A | Exp/2336005-A |
| CVE-2023-36391 | Exp/2336391-A | Exp/2336391-A |
| CVE-2023-36696 | Exp/2336696-A | Exp/2336696-A |
As you’ll be able to each month, for those who don’t need to wait on your system to tug down Microsoft’s updates itself, you’ll be able to obtain them manually from the Home windows Replace Catalog web site. Run the winver.exe software to find out which construct of Home windows 10 or 11 you’re operating, then obtain the Cumulative Replace package deal on your particular system’s structure and construct quantity.
Appendix A: Vulnerability Impression and Severity
It is a checklist of December’s patches sorted by impression, then sub-sorted by severity. Every checklist is additional organized by CVE.
Elevation of Privilege (10 CVEs)
| Necessary severity | |
| CVE-2023-35624 | Azure Linked Machine Agent Elevation of Privilege Vulnerability |
| CVE-2023-35631 | Win32k Elevation of Privilege Vulnerability |
| CVE-2023-35632 | Home windows Ancillary Perform Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2023-35633 | Home windows Kernel Elevation of Privilege Vulnerability |
| CVE-2023-35644 | Home windows Sysmain Service Elevation of Privilege |
| CVE-2023-36003 | XAML Diagnostics Elevation of Privilege Vulnerability |
| CVE-2023-36005 | Home windows Telephony Server Elevation of Privilege Vulnerability |
| CVE-2023-36011 | Win32k Elevation of Privilege Vulnerability |
| CVE-2023-36391 | Native Safety Authority Subsystem Service Elevation of Privilege Vulnerability |
| CVE-2023-36696 | Home windows Cloud Recordsdata Mini Filter Driver Elevation of Privilege Vulnerability |
Distant Code Execution (8 CVEs)
| Vital severity | |
| CVE-2023-35628 | Home windows MSHTML Platform Distant Code Execution Vulnerability |
| CVE-2023-35630 | Web Connection Sharing (ICS) Distant Code Execution Vulnerability |
| CVE-2023-35641 | Web Connection Sharing (ICS) Distant Code Execution Vulnerability |
| Necessary severity | |
| CVE-2023-21740 | Home windows Media Distant Code Execution Vulnerability |
| CVE-2023-35629 | Microsoft USBHUB 3.0 Machine Driver Distant Code Execution Vulnerability |
| CVE-2023-35634 | Home windows Bluetooth Driver Distant Code Execution Vulnerability |
| CVE-2023-35639 | Microsoft ODBC Driver Distant Code Execution Vulnerability |
| CVE-2023-36006 | Microsoft WDAC OLE DB supplier for SQL Server Distant Code Execution Vulnerability |
Spoofing (5 CVEs)
| Vital severity | |
| CVE-2023-36019 | Microsoft Energy Platform Connector Spoofing Vulnerability |
| Necessary severity | |
| CVE-2023-35619 | Microsoft Outlook for Mac Spoofing Vulnerability |
| CVE-2023-35622 | Home windows DNS Spoofing Vulnerability |
| CVE-2023-36004 | Home windows DPAPI (Information Safety Utility Programming Interface) Spoofing Vulnerability |
| CVE-2023-36020 | Microsoft Dynamics 365 (on-premises) Cross-site Scripting Vulnerability |
Denial of Service (5 CVEs)
| Necessary severity | |
| CVE-2023-35621 | Microsoft Dynamics 365 Finance and Operations Denial of Service Vulnerability |
| CVE-2023-35635 | Home windows Kernel Denial of Service Vulnerability |
| CVE-2023-35638 | DHCP Server Service Denial of Service Vulnerability |
| CVE-2023-35642 | Web Connection Sharing (ICS) Denial of Service Vulnerability |
| CVE-2023-36010 | Microsoft Defender Denial of Service Vulnerability |
Data Disclosure (5 CVEs)
| Necessary severity | |
| CVE-2023-35625 | Azure Machine Studying Compute Occasion for SDK Customers Data Disclosure Vulnerability |
| CVE-2023-35636 | Microsoft Outlook Data Disclosure Vulnerability |
| CVE-2023-35643 | DHCP Server Service Data Disclosure Vulnerability |
| CVE-2023-36009 | Microsoft Phrase Data Disclosure Vulnerability |
| CVE-2023-36012 | DHCP Server Service Data Disclosure Vulnerability |
Appendix B: Exploitability
It is a checklist of the December CVEs judged by Microsoft to be extra more likely to be exploited within the wild inside the first 30 days post-release. Every checklist is additional organized by CVE. No CVEs addressed within the December patch assortment are recognized to be underneath energetic exploit within the wild but.
| Exploitation extra probably inside 30 days | |
| CVE-2023-35628 | Home windows MSHTML Platform Distant Code Execution Vulnerability |
| CVE-2023-35631 | Win32k Elevation of Privilege Vulnerability |
| CVE-2023-35632 | Home windows Ancillary Perform Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2023-35633 | Home windows Kernel Elevation of Privilege Vulnerability |
| CVE-2023-35641 | Web Connection Sharing (ICS) Distant Code Execution Vulnerability |
| CVE-2023-35644 | Home windows Sysmain Service Elevation of Privilege |
| CVE-2023-36005 | Home windows Telephony Server Elevation of Privilege Vulnerability |
| CVE-2023-36010 | Microsoft Defender Denial of Service Vulnerability |
| CVE-2023-36011 | Win32k Elevation of Privilege Vulnerability |
| CVE-2023-36391 | Native Safety Authority Subsystem Service Elevation of Privilege Vulnerability |
| CVE-2023-36696 | Home windows Cloud Recordsdata Mini Filter Driver Elevation of Privilege Vulnerability |
Appendix C: Merchandise Affected
It is a checklist of December’s patches sorted by product household, then sub-sorted by severity. Every checklist is additional organized by CVE. Patches which can be shared amongst a number of product households are listed a number of instances, as soon as for every product household.
Home windows (24 CVEs)
| Vital severity | |
| CVE-2023-35628 | Home windows MSHTML Platform Distant Code Execution Vulnerability |
| CVE-2023-35630 | Web Connection Sharing (ICS) Distant Code Execution Vulnerability |
| CVE-2023-35641 | Web Connection Sharing (ICS) Distant Code Execution Vulnerability |
| Necessary severity | |
| CVE-2023-21740 | Home windows Media Distant Code Execution Vulnerability |
| CVE-2023-35622 | Home windows DNS Spoofing Vulnerability |
| CVE-2023-35629 | Microsoft USBHUB 3.0 Machine Driver Distant Code Execution Vulnerability |
| CVE-2023-35631 | Win32k Elevation of Privilege Vulnerability |
| CVE-2023-35632 | Home windows Ancillary Perform Driver for WinSock Elevation of Privilege Vulnerability |
| CVE-2023-35633 | Home windows Kernel Elevation of Privilege Vulnerability |
| CVE-2023-35634 | Home windows Bluetooth Driver Distant Code Execution Vulnerability |
| CVE-2023-35635 | Home windows Kernel Denial of Service Vulnerability |
| CVE-2023-35638 | DHCP Server Service Denial of Service Vulnerability |
| CVE-2023-35639 | Microsoft ODBC Driver Distant Code Execution Vulnerability |
| CVE-2023-35642 | Web Connection Sharing (ICS) Denial of Service Vulnerability |
| CVE-2023-35643 | DHCP Server Service Data Disclosure Vulnerability |
| CVE-2023-35644 | Home windows Sysmain Service Elevation of Privilege |
| CVE-2023-36003 | XAML Diagnostics Elevation of Privilege Vulnerability |
| CVE-2023-36004 | Home windows DPAPI (Information Safety Utility Programming Interface) Spoofing Vulnerability |
| CVE-2023-36005 | Home windows Telephony Server Elevation of Privilege Vulnerability |
| CVE-2023-36006 | Microsoft WDAC OLE DB supplier for SQL Server Distant Code Execution Vulnerability |
| CVE-2023-36011 | Win32k Elevation of Privilege Vulnerability |
| CVE-2023-36012 | DHCP Server Service Data Disclosure Vulnerability |
| CVE-2023-36391 | Native Safety Authority Subsystem Service Elevation of Privilege Vulnerability |
| CVE-2023-36696 | Home windows Cloud Recordsdata Mini Filter Driver Elevation of Privilege Vulnerability |
Azure (3 CVEs)
| Vital severity | |
| CVE-2023-36019 | Microsoft Energy Platform Connector Spoofing Vulnerability |
| Necessary severity | |
| CVE-2023-35624 | Azure Linked Machine Agent Elevation of Privilege Vulnerability |
| CVE-2023-35625 | Azure Machine Studying Compute Occasion for SDK Customers Data Disclosure Vulnerability |
Workplace (3 CVEs)
| Necessary severity | |
| CVE-2023-35619 | Microsoft Outlook for Mac Spoofing Vulnerability |
| CVE-2023-35636 | Microsoft Outlook Data Disclosure Vulnerability |
| CVE-2023-36009 | Microsoft Phrase Data Disclosure Vulnerability |
Dynamics 365 (2 CVEs)
| Necessary severity | |
| CVE-2023-35621 | Microsoft Dynamics 365 Finance and Operations Denial of Service Vulnerability |
| CVE-2023-36020 | Microsoft Dynamics 365 (on-premises) Cross-site Scripting Vulnerability |
Defender (1 CVE)
| Necessary severity | |
| CVE-2023-36010 | Microsoft Defender Denial of Service Vulnerability |
Energy Platform (1 CVE)
| Necessary severity | |
| CVE-2023-36019 | Microsoft Energy Platform Connector Spoofing Vulnerability |
Appendix D: Advisories and Different Merchandise
It is a checklist of advisories and data on different related CVEs within the December Microsoft launch, sorted by product.
Microsoft Servicing Stack Updates
| ADV990001 | Newest Servicing Stack Updates |
Related to Edge / Chromium (9 CVEs)
| CVE-2033-6508 | Chromium: CVE-2023-6508 Use after free in Media Stream |
| CVE-2023-6509 | Chromium: CVE-2023-6509 Use after free in Aspect Panel Search |
| CVE-2023-6510 | Chromium: CVE-2023-6510 Use after free in Media Seize |
| CVE-2023-6511 | Chromium: CVE-2023-6511 Inappropriate implementation in Autofill |
| CVE-2023-6512 | Chromium: CVE-2023-6512 Inappropriate implementation in Internet Browser UI |
| CVE-2023-35618 | Microsoft Edge (Chromium-based) Elevation of Privilege Vulnerability |
| CVE-2023-35637 | Microsoft Edge (Chromium-based) Safety Function Bypass Vulnerability |
| CVE-2023-36880 | Microsoft Edge (Chromium-based) Data Disclosure Vulnerability |
| CVE-2023-38174 | Microsoft Edge (Chromium-based) Data Disclosure Vulnerability |