E-mail safety instruments reminiscent of Safe E-mail Gateways (SEGs) typically encode URLs which might be embedded in emails. This allows the safety equipment to scan the URL earlier than the recipient visits the web site. Oftentimes when SEGs detect URLs in emails which might be already SEG encoded they don’t scan the URLs, or the scanning reveals solely the safety device’s scanning web page and never the precise vacation spot. Because of this, when an electronic mail already has SEG encoded URLs the recipient’s SEG typically permits the e-mail via with out correctly checking the embedded URLs. Menace actors have abused this for a while, however Q2 of this yr, and Could specifically, noticed a rise in risk actors benefiting from SEG encoding malicious URLs earlier than sending them to victims.
Instruments Utilized in The Wild
The 4 instruments mostly seen in use by risk actors to encode URLs and bypass SEGs in Q2 2024 are VIPRE E-mail Safety, BitDefender LinkScan, Hornet Safety Superior Menace Safety URL Rewriting, and Barracuda E-mail Gateway Protection Hyperlink Safety. E-mail campaigns utilizing these instruments to bypass SEGs have been seen in environments protected by all the things from Proofpoint to Microsoft ATP.
VIPRE E-mail Safety
URLs encoded by VIPRE E-mail Safety, particularly URLs encoded by url[.]emailprotection[.]hyperlink had been seen with 12 distinctive topics in early June 2024. These emails had topics just like the next subset:
| Frequent E-mail Topics |
| Overview & Signal: Partnership_Investment_Proposal.DOCX |
| New Contract and Termination Settlement.pdf |
| You will have a brand new encrypted VM from <recipient identify or identifiable info> |
| Full: Increment Coverage and Commonplace Termination Settlement.pdf. |
| Wage Compensation Report 2024 |
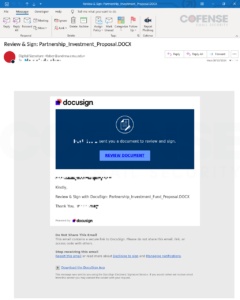
Determine 1: E-mail with embedded URL encoded by VIPRE E-mail Safety’s url[.]emailprotection[.]hyperlink.
URLs encoded with VIPRE E-mail Safety’s different encoding URLs: url2[.]mailanyone[.]internet, url10[.]mailanyone[.]internet, url12[.]mailanyone[.]internet, and so forth. had been seen primarily in Could of 2024 with over 200 distinctive topics. These emails had topics just like the next subset:
| Frequent E-mail Topics |
| 7167-<recipient identify or identifiable info>: Settle for the proposal and return |
| One Time Authentication Immediate |
| Notification Entry #27 -Could 15, 2024, 07:49:27 AM |
| 8533-<recipient identify or identifiable info>: Signal and Return to course of |
| <recipient identify or identifiable info> Termination Settlement……623.docx |

Determine 2: E-mail with embedded URL encoded by VIPRE E-mail Safety’s url10[.]mailanyone[.]internet.
BitDefender LinkScan
URLs encoded by BitDefender LinkScan, particularly URLs encoded by lsems[.]gravityzone[.]bitdefender[.]com had been seen most frequently in early June 2024 with 8 distinctive topics. These emails had topics just like the next subset:
| Frequent E-mail Topics |
| Pressing Motion Required: Safe E-mail Alert !!! |
| Oops, We Withheld Some Messages From you June 09 Case- #UMMQEGA7 |
| <recipient identify or identifiable info> e-Safe/e-File/0B6UCG Tuesday, June 11, 2024 |
| Timesheet Replace Notification: View Ref-VJ7N8GO012P modifications made to your timesheet |
| Report Ticket 0168724 For <recipient identify or identifiable info> |
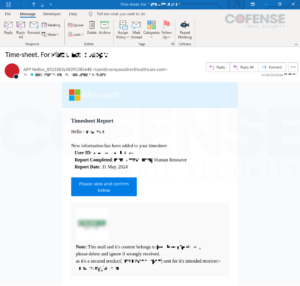
Determine 3: E-mail with embedded URL encoded by BitDefender LinkScan’s lsems[.]gravityzone[.]bitdefender[.]com.
URLs encoded with BitDefender LinkScan’s different encoding URL, linkscan[.]io, had been solely seen in two campaigns in June of 2024. These emails had topics just like the next subset:
| Frequent E-mail Topics |
| Fast Motion Required: Mail Server Error – Replace Entry on Tuesday 11/Jun/2024 – TicketID: LCCP-YLSNYA-FLLWK |
| Time-sheet For <recipient identify or identifiable info> |
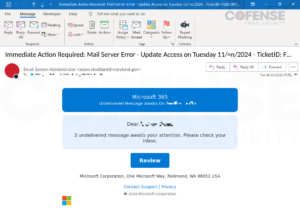
Determine 4: E-mail with embedded URL encoded by BitDefender LinkScan’s linkscan[.]io.
Hornet Safety Superior Menace Safety URL Rewriting
URLs encoded with Hornet Safety Superior Menace Safety URL Rewriting (seclinks[.]cloud-security[.]internet) had been seen primarily in late Could and early June of 2024 with 8 distinctive topics. These emails had topics just like the next subset:
| Frequent E-mail Topics |
| PVX #5LOA: Full: Please Signal&Return #Ref-D786DYY37B(2) |
| Oops, We Withheld Some Messages From you June 09 Case- #UMMQEGA7 |
| <recipient identify or identifiable info> e-Safe/e-File/0B6UCG Tuesday, June 11, 2024 |
| Timesheet Replace Notification: View Ref-VJ7N8GO012P modifications made to your timesheet |
| Time-sheet Submission: Please affirm your new time-sheet |

Determine 5: E-mail with embedded URL encoded by Hornet Safety Superior Menace Safety URL Rewriting’s seclinks[.]cloud-security[.]internet.
URLs encoded with Hornet Safety Superior Menace Safety URL Rewriting’s different encoding URL, atpscan[.]world[.]hornetsecurity[.]com, had been solely seen in campaigns in late Could and early June of 2024 with 16 distinctive topics. These emails had topics just like the next subset:
| Frequent E-mail Topics |
| Authorised for under 83574 – <recipient identify or identifiable info> |
| #0IU6IB Overview Monday, June 10, 2024 |
| YV8 72Q: Signal&Return #Ref-JB0UOYAY19P |
| 4700-27Z Please full: Signal&Return #Ref-04020427Z |
| Motion Required: We witheld 9 messages from you. |

Determine 6: E-mail with embedded URL encoded by Hornet Safety Superior Menace Safety URL Rewriting’s atpscan[.]world[.]hornetsecurity[.]com.
Barracuda E-mail Gateway Protection Hyperlink Safety
URLs encoded by Barracuda E-mail Gateway Protection Hyperlink Safety, particularly URLs encoded by linkprotect[.]cudasvc[.]com had been seen with 19 distinctive topics in Q2 2024. These emails had topics just like the next subset:
| Frequent E-mail Topics |
| #23321041 |
| Your DocXXX Await Your Approval Ref:#ezgyo4r |
| Complete Wellness Program for <recipient identify or identifiable info> Staff |
| Your DocXXX Await Your Approval Ref:#hlufnew |

Determine 7: E-mail with embedded URL encoded by Barracuda E-mail Gateway Protection Hyperlink Safety’s linkprotect[.]cudasvc[.]com.
Varieties Of Campaigns Seen Utilizing SEG Encoded URLs
There have been many several types of campaigns making use of SEG encoded URLs in Q2. Among the most typical themes had been content material requiring a signature and voicemail or withheld electronic mail notifications. As will be seen from the above Figures, DocuSign and Microsoft had been typically spoofed.
DocuSign
A lot of campaigns themed round content material requiring a signature spoofed DocuSign. Regardless of this spoofing, comparatively few of the campaigns made use of an precise DocuSign hyperlink which isn’t unusual amongst Credential Phishing emails spoofing DocuSign. That is possible as a result of the DocuSign hyperlinks are sometimes used to bypass SEGs and if the risk actor is already bypassing a SEG by encoding the malicious URL then they haven’t any want for an additional step that may get taken down.
Microsoft
Second solely to DocuSign, Microsoft was probably the most generally spoofed model in electronic mail campaigns making use of SEG encoded URLs in Q2 2024. Though not all of the Microsoft spoofing made sense, for instance, the Microsoft spoofing Time Sheet Report in Determine 3, it was nonetheless generally seen. It is a widespread tactic for risk actors in search of to abuse victims’ inherent belief in well-known manufacturers.