Three-quarters of business corporations suffered a ransomware assault up to now 12 months, with much more compromises affecting operational know-how (OT) than ever earlier than — representing a surge in assaults pushed by each the commercial sector’s vulnerability and propensity to pay ransoms to be able to stay operational.
Up to now 12 months, greater than half of business corporations (54%) suffered a ransomware assault that impacted their operational know-how, whether or not immediately or as a result of a linked IT system had been attacked, in keeping with a report launched by cyber-physical protection firm Claroty on Dec. 6. The affect of the assaults on OT techniques is a notable enhance from the agency’s final report in 2021, when 47% of corporations had ransomware affect their operations.
Certainly, assaults on industrial corporations and demanding infrastructure suppliers have change into downright widespread. The Aliquippa Municipal Water Authority, positioned in Pittsburgh, lately suffered a web site defacement after an Iranian-linked risk group referred to as Cyber Av3ngers compelled it to close down a water-pressure monitoring system and adjusted the positioning’s touchdown web page. That incident turned out to be a part of a wider spate of cyberattacks on water amenities throughout the US that began in late November. Nevertheless it’s not simply utilities within the sights: in February 2022, tire maker Bridgestone needed to shut down its manufacturing networks for a number of days after the LockBit 2.0 ransomware group efficiently breached its community.
Whereas the Claroty survey reveals that direct focusing on of OT techniques remained constant over the 2 time durations, with greater than a 3rd of corporations (37%) struggling assaults that affected each IT and OT techniques in 2023, there was a big enhance from the 27% of organizations struggling dual-impact assaults in 2021, say Grant Geyer, chief product officer at Claroty.
“The numbers — as astounding as they have been final 12 months — they proceed to not solely present the severity of the issue, however the truth that it is a particularly viable enterprise mannequin and places operations in danger, not simply IT,” he says. “As a result of so many OT techniques are Home windows-based, the ransomware usually spills over from the IT setting into the OT setting, due to poor or no segmentation.”
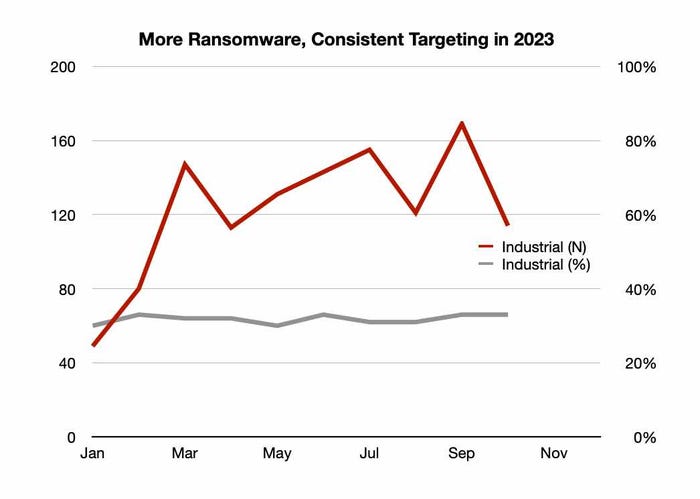
Whereas the variety of ransomware incidents in opposition to industrial corporations has elevated, they persistently account for a 3rd of all assaults. Supply: NCC Group.
General, the commercial sector has remained the highest ransomware goal each month for the previous 12 months, in keeping with information from the NCC Group, a cybersecurity companies agency. Ransomware assaults have been up 81% in October, in comparison with the identical month the earlier 12 months, and assaults on the commercial sector routinely signify a 3rd of all ransomware incidents.
Menace exercise has additionally elevated general due to current geo-political conflicts, resulting in industrial assaults by each state-sponsored actors and hacktivists, says Sean Arrowsmith, head of Industrials for the NCC Group.
“The power to disable, and or cripple power infrastructure can lead to restricted to no entry for its customers, including to the instability and chaos that warfare and battle deliver,” he says. “These acts of sabotage play into the all-important energy dynamics of worldwide safety points.”
Industrials to Attackers: “Hey, We’ll Pay”
One purpose for the attractiveness of attacking industrial corporations: disruptions to operations lead to a higher chance of pay ransoms. Sometimes, corporations’ propensity to pay ransomware relies upon closely on their income — smaller corporations pay up 36% of the time, as an alternative counting on backups, whereas bigger corporations pay 55% of the time, in keeping with Sophos’ annual State of Ransomware report.
In the meantime, victims within the industrial sector pay a whopping two-thirds (67%) of the time, in keeping with Claroty’s World State of Industrial Cybersecurity 2023 report.
“It’s a must to look no additional than the truth that two-thirds of organizations are paying the ransom to acknowledge why so many organizations are being attacked,” Claroty’s Geyer says. “Operational outages places CIOs between a rock and a tough place, and forces them to make these untenable emotional choices.”
Third events are one other weak point that corporations reliant on OT — comparable to industrial corporations and utilities — want to deal with.
All High-10 power corporations in the USA, for instance, had a third-party supplier that suffered a compromise up to now 12 months, resulting in a breach of their enterprise, in keeping with safety metrics agency SecurityScorecard. Whereas solely 4% of the almost 2,000 third-party suppliers tracked by the agency suffered a direct compromise, that led to 90% of power corporations worldwide coping with the fallout of these breaches over a 12 months.
Working example, the MOVEit breach alone affected lots of of power corporations, in keeping with Rob Ames, employees risk researcher at SecurityScorecard.
“This type of declare of a breach after which threatened information publicity is turning into a more-and-more central a part of the publicity of the extortion try, slightly than the precise deployment of ransomware correctly,” he says. “I might say that extortion makes an attempt that rely extra on claimed publicity, slightly than precise encryption is a development, and, in fact, nonetheless financially motivated.”
Extra Authorities Assist Vital for OT Safety
Many water utilities and different crucial infrastructure corporations are small, native corporations, or operated by cities and counties. As such, they are usually behind on deploying cybersecurity. Working example: two years after the ransomware assault on Colonial Pipeline, crucial infrastructure homeowners are nonetheless not prepared to guard in opposition to ransomware, actually because the economics doesn’t add up, says Claroty’s Geyer.
“Free-market forces in sure segments cannot economically drive change to a few of these least protected/most weak points of our society,” he says. “And that is the chance for complete of presidency to step in and never simply drive regulation, however drive funding to assist make sure that many of those entities under-invested in cyber — what we name ‘goal wealthy, cyber poor’ sectors — are correctly defended.”
Corporations don’t must have deep experience in-house, however ought to give attention to visibility, planning, and incident response workout routines, says NCC Group’s Arrowsmith.
“Develop a strong incident-response plan for IT and OT, then rehearse and drill that plan so all stakeholders are clear on roles and duties,” he says.

