As builders proceed to construct better autonomy into cyber-physical methods (CPSs), corresponding to unmanned aerial autos (UAVs) and vehicles, these methods mixture information from an rising variety of sensors. The methods use this information for management and for in any other case appearing of their operational environments. Nonetheless, extra sensors not solely create extra information and extra exact information, however they require a fancy structure to accurately switch and course of a number of information streams. This improve in complexity comes with extra challenges for purposeful verification and validation (V&V) a better potential for faults (errors and failures), and a bigger assault floor. What’s extra, CPSs usually can not distinguish faults from assaults.
To deal with these challenges, researchers from the SEI and Georgia Tech collaborated on an effort to map the issue area and develop proposals for fixing the challenges of accelerating sensor information in CPSs. This SEI Weblog put up supplies a abstract our work, which comprised analysis threads addressing 4 subcomponents of the issue:
- addressing error propagation induced by studying parts
- mapping fault and assault eventualities to the corresponding detection mechanisms
- defining a safety index of the power to detect tampering based mostly on the monitoring of particular bodily parameters
- figuring out the affect of clock offset on the precision of reinforcement studying (RL)
Later I’ll describe these analysis threads, that are half of a bigger physique of analysis we name Security Evaluation and Fault Detection Isolation and Restoration (SAFIR) Synthesis for Time-Delicate Cyber-Bodily Techniques. First, let’s take a more in-depth take a look at the issue area and the challenges we’re working to beat.
Extra Information, Extra Issues
CPS builders need extra and higher information so their methods could make higher choices and extra exact evaluations of their operational environments. To attain these targets, builders add extra sensors to their methods and enhance the power of those sensors to collect extra information. Nonetheless, feeding the system extra information has a number of implications: extra information means the system should execute extra, and extra complicated, computations. Consequently, these data-enhanced methods want extra highly effective central processing models (CPUs).
Extra highly effective CPUs introduce numerous issues, corresponding to vitality administration and system reliability. Bigger CPUs additionally elevate questions on electrical demand and electromagnetic compatibility (i.e., the power of the system to face up to electromagnetic disturbances, corresponding to storms or adversarial interference).
The addition of latest sensors means methods must mixture extra information streams. This want drives better architectural complexity. Furthermore, the information streams have to be synchronized. As an illustration, the data obtained from the left facet of an autonomous vehicle should arrive concurrently data coming from the suitable facet.
Extra sensors, extra information, and a extra complicated structure additionally elevate challenges in regards to the security, safety, and efficiency of those methods, whose interplay with the bodily world raises the stakes. CPS builders face heightened strain to make sure that the information on which their methods rely is correct, that it arrives on schedule, and that an exterior actor has not tampered with it.
A Query of Belief
As builders attempt to imbue CPSs with better autonomy, one of many largest hurdles is gaining the belief of customers who rely upon these methods to function safely and securely. For instance, take into account one thing so simple as the air strain sensor in your automobile’s tires. Up to now, we needed to examine the tires bodily, with an air strain gauge, usually miles after we’d been driving on tires dangerously underinflated. The sensors we’ve got in the present day tell us in actual time when we have to add air. Over time, we’ve got come to rely upon these sensors. Nonetheless, the second we get a false alert telling us our entrance driver’s facet tire is underinflated, we lose belief within the capability of the sensors to do their job.
Now, take into account an analogous system wherein the sensors cross their data wirelessly, and a flat-tire warning triggers a security operation that forestalls the automobile from beginning. A malicious actor learns how one can generate a false alert from a spot throughout the parking zone or merely jams your system. Your tires are high-quality, your automobile is okay, however your automobile’s sensors, both detecting a simulated drawback or completely incapacitated, is not going to allow you to begin the automobile. Prolong this situation to autonomous methods working in airplanes, public transportation methods, or massive manufacturing amenities, and belief in autonomous CPSs turns into much more crucial.
As these examples reveal, CPSs are vulnerable to each inside faults and exterior assaults from malicious adversaries. Examples of the latter embrace the Maroochy Shire incident involving sewage providers in Australia in 2000, the Stuxnet assaults focusing on energy crops in 2010, and the Keylogger virus towards a U.S. drone fleet in 2011.
Belief is crucial, and it lies on the coronary heart of the work we’ve got been doing with Georgia Tech. It’s a multidisciplinary drawback. In the end, what builders search to ship is not only a bit of {hardware} or software program, however a cyber-physical system comprising each {hardware} and software program. Builders want an assurance case, a convincing argument that may be understood by an exterior celebration. The reassurance case should reveal that the way in which the system was engineered and examined is per the underlying theories used to collect proof supporting the security and safety of the system. Making such an assurance case doable was a key a part of the work described within the following sections.
Addressing Error Propagation Induced by Studying Elements
As I famous above, autonomous CPSs are complicated platforms that function in each the bodily and cyber domains. They make use of a mixture of completely different studying parts that inform particular synthetic intelligence (AI) features. Studying parts collect information concerning the setting and the system to assist the system make corrections and enhance its efficiency.
To attain the extent of autonomy wanted by CPSs when working in unsure or adversarial environments, CPSs make use of studying algorithms. These algorithms use information collected by the system—earlier than or throughout runtime—to allow choice making and not using a human within the loop. The educational course of itself, nonetheless, shouldn’t be with out issues, and errors could be launched by stochastic faults, malicious exercise, or human error.
Many teams are engaged on the issue of verifying studying parts. Normally, they’re within the correctness of the training element itself. This line of analysis goals to provide an integration-ready element that has been verified with some stochastic properties, corresponding to a probabilistic property. Nonetheless, the work we performed on this analysis thread examines the issue of integrating a learning-enabled element inside a system.
For instance, we ask, How can we outline the structure of the system in order that we will fence off any learning-enabled element and assess that the information it’s receiving is right and arriving on the proper time? Moreover, Can we assess that the system outputs could be managed for some notion of correctness? As an illustration, Is the acceleration of my automobile throughout the pace restrict? This type of fencing is important to find out whether or not we will belief that the system itself is right (or, a minimum of, not that flawed) in comparison with the verification of a operating element, which in the present day shouldn’t be doable.
To deal with these questions, we described the varied errors that may seem in CPS parts and have an effect on the training course of. We additionally offered theoretical instruments that can be utilized to confirm the presence of such errors. Our purpose was to create a framework that operators of CPSs can use to evaluate their operation when utilizing data-driven studying parts. To take action, we adopted a divide-and-conquer strategy that used the Structure Evaluation & Design Language (AADL) to create a illustration of the system’s parts, and their interconnections, to assemble a modular setting that allowed for the inclusion of various detection and studying mechanisms. This strategy helps a full model-based growth, together with system specification, evaluation, system tuning, integration, and improve over the lifecycle.
We used a UAV system for instance how errors propagate all through system parts when adversaries assault the training processes and acquire security tolerance thresholds. We targeted solely on particular studying algorithms and detection mechanisms. We then investigated their properties of convergence, in addition to the errors that may disrupt these properties.
The outcomes of this investigation present the place to begin for a CPS designer’s information to using AADL for system-level evaluation, tuning, and improve in a modular vogue. This information may comprehensively describe the completely different errors within the studying processes throughout system operation. With these descriptions, the designer can mechanically confirm the right operation of the CPS by quantifying marginal errors and integrating the system into AADL to judge crucial properties in all lifecycle phases. To study extra about our strategy, I encourage you to learn the paper A Modular Method to Verification of Studying Elements in Cyber-Bodily Techniques.
Mapping Fault and Assault Eventualities to Corresponding Detection Mechanisms
UAVs have develop into extra vulnerable to each stochastic faults (stemming from faults occurring on the different parts comprising the system) and malicious assaults that compromise both the bodily parts (sensors, actuators, airframe, and many others.) or the software program coordinating their operation. Different analysis communities, utilizing an assortment of instruments which are usually incompatible with one another, have been investigating the causes and effects of faults that happen in UAVs. On this analysis thread, we sought to determine the core properties and components of those approaches to decompose them and thereby allow designers of UAV methods to think about all of the different outcomes on faults and the related detection strategies through an built-in algorithmic strategy. In different phrases, in case your system is below assault, how do you choose the very best mechanism for detecting that assault?
The problem of faults and assaults on UAVs has been broadly studied, and a lot of taxonomies have been proposed to assist engineers design mitigation methods for numerous assaults. In our view, nonetheless, these taxonomies had been insufficient. We proposed a choice course of product of two components: first, a mapping from fault or assault eventualities to summary error varieties, and second, a survey of detection mechanisms based mostly on the summary error varieties they assist detect. Utilizing this strategy, designers may use each components to pick a detection mechanism to guard the system.
To categorise the assaults on UAVs, we created an inventory of element compromises, specializing in people who reside on the intersection of the bodily and the digital realms. The checklist is way from complete, however it’s enough for representing the main qualities that describe the effects of these assaults to the system. We contextualized the checklist by way of assaults and faults on sensing, actuating, and communication parts, and extra complicated assaults focusing on a number of components to trigger system-wide errors:
|
|
|
|
|
|
|
Utilizing this checklist of assaults on UAVs and people on UAV platforms, we subsequent recognized their properties by way of the taxonomy standards launched by the SEI’s Sam Procter and Peter Feiler in The AADL Error Library: An Operationalized Taxonomy of System Errors. Their taxonomy supplies a set of information phrases to explain errors based mostly on their class: worth, timing, amount, and many others. Desk 1 presents a subset of these courses as they apply to UAV faults and assaults.
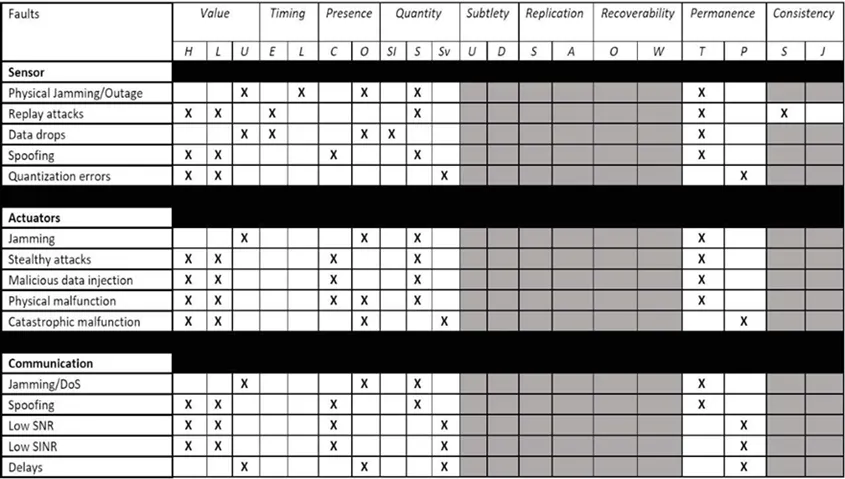
Determine 1: Classification of Assaults and Faults on UAVs Primarily based on the EMV2 Error Taxonomy
We then created a taxonomy of detection mechanisms that included statistics-based, sample-based, and Bellman-based intrusion detection methods. We associated these mechanisms to the assaults and faults taxonomy. Utilizing these examples, we developed a decision-making course of and illustrated it with a situation involving a UAV system. On this situation, the car undertook a mission wherein it confronted a excessive likelihood of being topic to an acoustic injection assault.
In such an assault, an analyst would check with the desk containing the properties of the assault and select the summary assault class of the acoustic injection from the assault taxonomy. Given the character of the assault, the suitable selection can be the spoofing sensor assault. Primarily based on the properties given by the assault taxonomy desk, the analyst would be capable of determine the important thing traits of the assault. Cross-referencing the properties of the assault with the span of detectable traits of the different intrusion detection mechanisms will decide the subset of mechanisms that can be profitable in environments with these forms of assaults.
On this analysis thread, we created a software that may assist UAV operators choose the suitable detection mechanisms for his or her system. Future work will concentrate on implementing the proposed taxonomy on a specific UAV platform, the place the precise sources of the assaults and faults could be explicitly identified on a low architectural stage. To study extra about our work on this analysis thread, I encourage you to learn the paper In the direction of Clever Safety for Unmanned Aerial Autos: A Taxonomy of Assaults, Faults, and Detection Mechanisms.
Defining a Safety Index of the Capability to Detect Tampering by Monitoring Particular Bodily Parameters
CPSs have steadily develop into massive scale and decentralized in recent times, and so they rely increasingly on communication networks. This high-dimensional and decentralized construction will increase the publicity to malicious assaults that may trigger faults, failures, and even vital harm. Analysis efforts have been made on the cost-efficient placement or allocation of actuators and sensors. Nonetheless, most of those developed strategies primarily take into account controllability or observability properties and don’t bear in mind the safety facet.
Motivated by this hole, we thought-about on this analysis thread the dependence of CPS safety on the possibly compromised actuators and sensors, specifically, on deriving a safety measure below each actuator and sensor assaults. The subject of CPS safety has obtained rising consideration lately, and completely different safety indices have been developed. The primary type of safety measure relies on reachability evaluation, which quantifies the scale of reachable units (i.e., the units of all states reachable by dynamical methods with admissible inputs). Thus far, nonetheless, little work has quantified reachable units below malicious assaults and used the developed safety metrics to information actuator and sensor choice. The second type of safety index is outlined because the minimal variety of actuators and/or sensors that attackers must compromise with out being detected.
On this analysis thread, we developed a generic actuator safety index. We additionally proposed graph-theoretic circumstances for computing the index with the assistance of most linking and the generic regular rank of the corresponding structured switch operate matrix. Our contribution right here was twofold. We offered circumstances for the existence of dynamical and ideal undetectability. By way of good undetectability, we proposed a safety index for discrete-time linear-time invariant (LTI) methods below actuator and sensor assaults. Then, we developed a graph-theoretic strategy for structured methods that’s used to compute the safety index by fixing a min-cut/max-flow drawback. For an in depth presentation of this work, I encourage you to learn the paper A Graph-Theoretic Safety Index Primarily based on Undetectability for Cyber-Bodily Techniques.
Figuring out the Impression of Clock Offset on the Precision of Reinforcement Studying
A serious problem in autonomous CPSs is integrating extra sensors and information with out lowering the pace of efficiency. CPSs, corresponding to automobiles, ships, and planes, all have timing constraints that may be catastrophic if missed. Complicating issues, timing acts in two instructions: timing to react to exterior occasions and timing to interact with people to make sure their safety. These circumstances elevate a lot of challenges as a result of timing, accuracy, and precision are traits key to making sure belief in a system.
Strategies for the event of safe-by-design methods have been principally targeted on the standard of the data within the community (i.e., within the mitigation of corrupted alerts both attributable to stochastic faults or malicious manipulation by adversaries). Nonetheless, the decentralized nature of a CPS requires the event of strategies that deal with timing discrepancies amongst its parts. Problems with timing have been addressed in management methods to evaluate their robustness towards such faults, but the consequences of timing points on studying mechanisms are hardly ever thought-about.
Motivated by this reality, our work on this analysis thread investigated the conduct of a system with reinforcement studying (RL) capabilities below clock offsets. We targeted on the derivation of ensures of convergence for the corresponding studying algorithm, on condition that the CPS suffers from discrepancies within the management and measurement timestamps. Particularly, we investigated the impact of sensor-actuator clock offsets on RL-enabled CPSs. We thought-about an off-policy RL algorithm that receives information from the system’s sensors and actuators and makes use of them to approximate a desired optimum management coverage.
However, owing to timing mismatches, the control-state information obtained from these system parts had been inconsistent and raised questions on RL robustness. After an in depth evaluation, we confirmed that RL does retain its robustness in an epsilon-delta sense. On condition that the sensor–actuator clock offsets are usually not arbitrarily massive and that the behavioral management enter satisfies a Lipschitz continuity situation, RL converges epsilon-close to the specified optimum management coverage. We performed a two-link manipulator, which clarified and verified our theoretical findings. For an entire dialogue of this work, I encourage you to learn the paper Impression of Sensor and Actuator Clock Offsets on Reinforcement Studying.
Constructing a Chain of Belief in CPS Structure
In conducting this analysis, the SEI has made some contributions within the subject of CPS structure. First, we prolonged AADL to make a proper semantics we will use not solely to simulate a mannequin in a really exact method, but in addition to confirm properties on AADL fashions. That work permits us to motive concerning the structure of CPSs. One consequence of this reasoning related to assuring autonomous CPSs was the thought of building a “fence” round susceptible parts. Nonetheless, we nonetheless wanted to carry out fault detection to verify inputs are usually not incorrect or tampered with or the outputs invalid.
Fault detection is the place our collaborators from Georgia Tech made key contributions. They’ve carried out nice work on statistics-based strategies for detecting faults and developed methods that use reinforcement studying to construct fault detection mechanisms. These mechanisms search for particular patterns that symbolize both a cyber assault or a fault within the system. They’ve additionally addressed the query of recursion in conditions wherein a studying element learns from one other studying element (which can itself be flawed). Kyriakos Vamvoudakis of Georgia Tech’s Daniel Guggenheim College of Aerospace Engineering labored out how one can use structure patterns to deal with these questions by increasing the fence round these parts. This work helped us implement and take a look at fault detection, isolation, and recording mechanism on use-case missions that we applied on a UAV platform.
We have now discovered that when you shouldn’t have a great CPS structure—one that’s modular, meets desired properties, and isolates fault tolerance—it’s essential to have a giant fence. It’s a must to do extra processing to confirm the system and acquire belief. However, you probably have an structure you can confirm is amenable to those fault tolerance strategies, then you may add within the fault isolation tolerances with out degrading efficiency. It’s a tradeoff.
One of many issues we’ve got been engaged on on this challenge is a group of design patterns which are recognized within the security group for detecting and mitigating faults utilizing a simplex structure to change from one model of a element to a different. We have to outline the aforementioned tradeoff for every of these patterns. As an illustration, patterns will differ within the variety of redundant parts, and, as we all know, extra redundancy is extra pricey as a result of we’d like extra CPU, extra wires, extra vitality. Some patterns will take extra time to decide or swap from nominal mode to degraded mode. We’re evaluating all these patterns, taking into account the price to implement them by way of sources—principally {hardware} sources—and the timing facet (the time between detecting an occasion to reconfiguring the system). These sensible issues are what we wish to deal with—not only a formal semantics of AADL, which is good for laptop scientists, but in addition this tradeoff evaluation made doable by offering a cautious analysis of each sample that has been documented within the literature.
In future work, we wish to deal with these bigger questions:
- What can we do with fashions after we do model-based software program engineering?
- How far can we go to construct a toolbox in order that designing a system could be supported by proof throughout each section?
- You wish to construct the structure of a system, however are you able to make sense of a diagram?
- What are you able to say concerning the security of the timing of the system?
The work is grounded on the imaginative and prescient of rigorous model-based methods engineering progressing from necessities to a mannequin. Builders additionally want supporting proof they will use to construct a belief package deal for an exterior auditor, to reveal that the system they designed works. In the end, our purpose is to construct a series of belief throughout all of a CPS’s engineering artifacts.