A Chinese language-speaking risk actor codenamed GoldFactory has been attributed to the event of extremely subtle banking trojans, together with a beforehand undocumented iOS malware referred to as GoldPickaxe that is able to harvesting identification paperwork, facial recognition knowledge, and intercepting SMS.
“The GoldPickaxe household is obtainable for each iOS and Android platforms,” Singapore-headquartered Group-IB stated in an intensive report shared with The Hacker Information. “GoldFactory is believed to be a well-organized Chinese language-speaking cybercrime group with shut connections to Gigabud.”
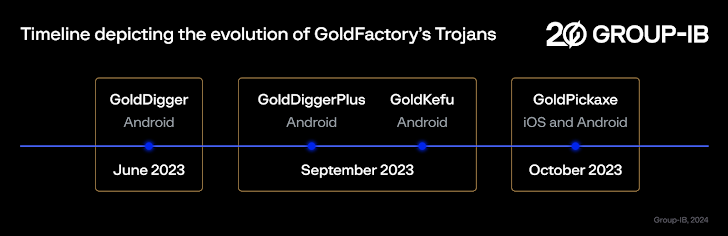
Energetic since not less than mid-2023, GoldFactory can also be liable for one other Android-based banking malware referred to as GoldDigger and its enhanced variant GoldDiggerPlus in addition to GoldKefu, an embedded trojan inside GoldDiggerPlus.
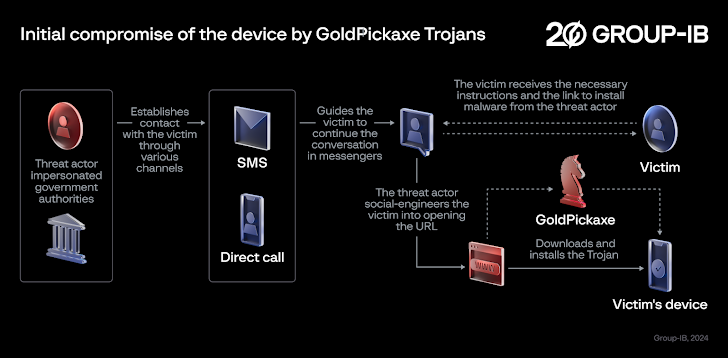
Social engineering campaigns distributing the malware have been discovered to focus on the Asia-Pacific area, particularly Thailand and Vietnam, by masquerading as native banks and authorities organizations.
In these assaults, potential victims are despatched smishing and phishing messages and guided to modify the dialog to instantaneous messaging apps like LINE, earlier than sending bogus URLs that result in the deployment of GoldPickaxe on the units.
A few of these malicious apps concentrating on Android are hosted on counterfeit web sites resembling Google Play Retailer pages or pretend company web sites to finish the set up course of.
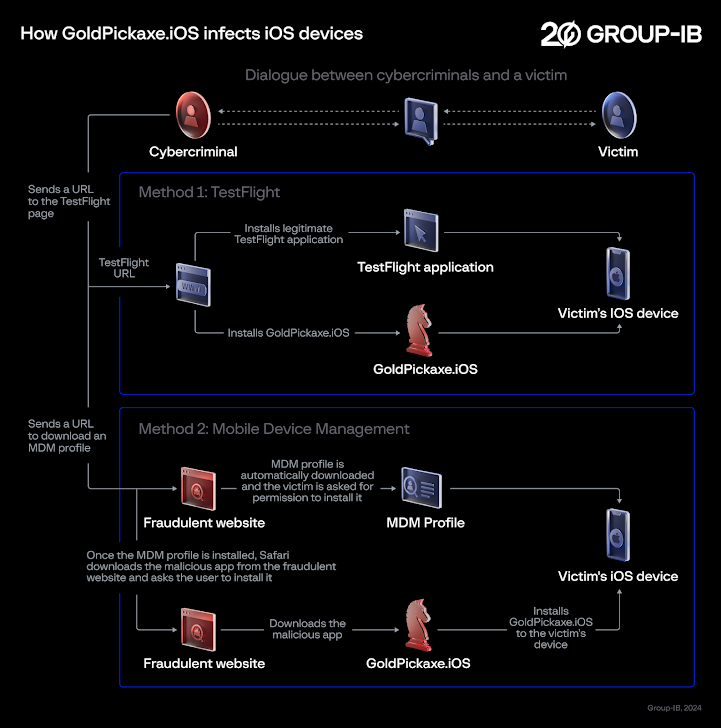
GoldPickaxe for iOS, nevertheless, employs a special distribution scheme, with successive iterations leveraging Apple’s TestFlight platform and booby-trapped URLs that immediate customers to obtain an Cell Machine Administration (MDM) profile to grant full management over the iOS units and set up the rogue app.
Each these propagation mechanisms have been disclosed by the Thailand Banking Sector CERT (TB-CERT) and the Cyber Crime Investigation Bureau (CCIB), respectively, in November 2023.
The sophistication of GoldPickaxe can also be evident in the truth that it is designed to get round safety measures imposed by Thailand that require customers to verify bigger transactions utilizing facial recognition to forestall fraud.
“GoldPickaxe prompts the sufferer to report a video as a affirmation methodology within the pretend software,” safety researchers Andrey Polovinkin and Sharmine Low stated. “The recorded video is then used as uncooked materials for the creation of deepfake movies facilitated by face-swapping synthetic intelligence providers.”
Moreover, the Android and iOS flavors of the malware are geared up to gather the sufferer’s ID paperwork and pictures, intercept incoming SMS messages, and proxy site visitors via the compromised system. It is suspected that the GoldFactory actors use their very own units to sign-in to the financial institution software and carry out unauthorized fund transfers.
That having stated, the iOS variant reveals fewer functionalities when in comparison with its Android counterpart owing to the closed nature of the iOS working system and comparatively stricter nature of iOS permissions.
The Android model – thought of an evolutionary successor of GoldDiggerPlus – additionally poses as over 20 completely different functions from Thailand’s authorities, the monetary sector, and utility corporations to steal login credentials from these providers. Nonetheless, it is at present not clear what the risk actors do with this info.
One other notable facet of the malware is its abuse of Android’s accessibility providers to log keystrokes and extract on-screen content material.
GoldDigger additionally shares code-level similarities to GoldPickaxe, though it’s mainly designed to steal banking credentials, whereas the latter is geared extra in the direction of gathering of non-public info from victims. No GoldDigger artifacts geared toward iOS units have been recognized up to now.
“The first function of GoldDigger is that it targets over 50 functions from Vietnamese monetary corporations, together with their packages’ names within the trojan,” the researchers stated. “Every time the focused functions open, it should save the textual content displayed or written on the UI, together with passwords, when they’re entered.”
The bottom model of GoldDigger, which was first found in June 2023 and continues to be nonetheless in circulation, has since paved the best way for extra upgraded variants, together with GoldDiggerPlus, which comes embedded with one other trojan APK part dubbed GoldKefu, to unleash the malicious actions.
GoldDiggerPlus is claimed to have emerged in September 2023, with GoldKefu impersonating a well-liked Vietnamese messaging app to siphon banking credentials related to 10 monetary establishments.
The Android trojan, which is used along with GoldKefu, makes use of pretend overlays to gather the login info if essentially the most not too long ago opened software belongs to the goal checklist, in contrast to GoldDigger which depends primarily on Android’s accessibility providers.
Goldkefu additionally integrates with the Agora Software program Growth Equipment (SDK) to facilitate interactive voice and video calls and trick victims into contacting a bogus financial institution customer support by sending pretend alerts that induce a false sense of urgency by claiming {that a} fund switch to the tune of three million Thai Baht has taken place on their accounts.
If something, the event is an indication that the cell malware panorama stays a profitable marketplace for cybercriminals on the lookout for fast monetary acquire, whilst they discover methods to bypass defensive measures erected by banks to counter such threats. It additionally demonstrates the ever-shifting and dynamic nature of social engineering schemes that purpose to ship malware to victims’ units.
To mitigate the dangers posed by GoldFactory and its suite of cell banking malware, it is strongly suggested to not click on on suspicious hyperlinks, set up any app from untrusted websites, as they’re a typical vector for malware, and periodically assessment the permissions given to apps, significantly these requesting for Android’s accessibility providers.
“GoldFactory is a resourceful staff adept at varied techniques, together with impersonation, accessibility keylogging, pretend banking web sites, pretend financial institution alerts, pretend name screens, identification, and facial recognition knowledge assortment,” the researchers stated. “The staff contains separate growth and operator teams devoted to particular areas.”
“The gang has well-defined processes and operational maturity and continuously enhances its toolset to align with the focused surroundings showcasing a excessive proficiency in malware growth.”