Customers of Mirth Join, an open-source information integration platform from NextGen HealthCare, are being urged to replace to the most recent model following the invention of an unauthenticated distant code execution vulnerability.
Tracked as CVE-2023-43208, the vulnerability has been addressed in model 4.4.1 launched on October 6, 2023.
“That is an simply exploitable, unauthenticated distant code execution vulnerability,” Horizon3.ai’s Naveen Sunkavally stated in a Wednesday report. “Attackers would most definitely exploit this vulnerability for preliminary entry or to compromise delicate healthcare information.”
Referred to as the “Swiss Military knife of healthcare integration,” Mirth Join is a cross-platform interface engine used within the healthcare trade to speak and trade information between disparate programs in a standardized method.
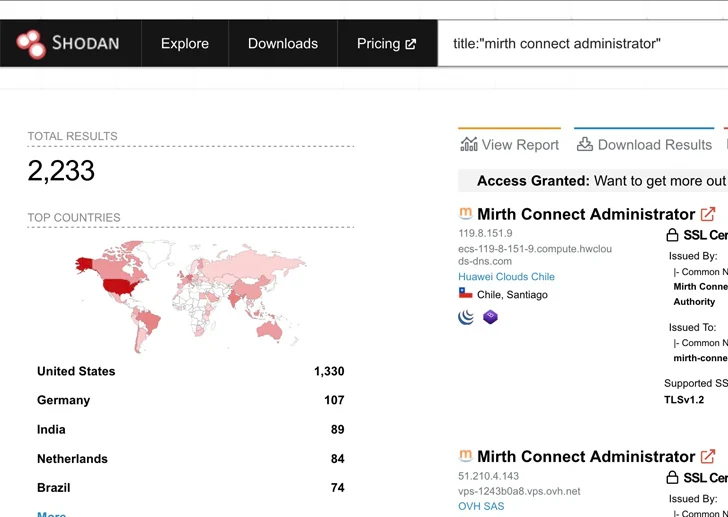
Further technical particulars in regards to the flaw have been withheld in mild of the truth that Mirth Join variations going way back to 2015/2016 have been discovered to be weak to the difficulty.
It is value noting that CVE-2023-43208 is a patch bypass for CVE-2023-37679 (CVSS rating: 9.8), a important distant command execution (RCE) vulnerability within the software program that enables attackers to execute arbitrary instructions on the internet hosting server.
Whereas CVE-2023-37679 was described by its maintainers as solely affecting servers working Java 8, Horizon3.ai’s evaluation discovered that each one situations of Mirth Join, whatever the Java model, have been inclined to the issue.
Given the benefit with which the vulnerability will be trivially abused, coupled with the truth that the exploitation strategies are well-known, it is advisable to replace Mirth Join, significantly which might be publicly accessible over the web, to model 4.4.1 as quickly as potential to mitigate potential threats.