Introduction
The trendy software program provide chain represents an ever-evolving menace panorama, with every bundle added to the manifest introducing new assault vectors. To satisfy trade necessities, organizations should preserve a fast-paced growth course of whereas staying up-to-date with the most recent safety patches. Nevertheless, in follow, builders usually face a considerable amount of safety work with out clear prioritization – and miss a good portion of the assault floor altogether.
The first problem arises from the detection and prioritization strategies utilized by conventional Static Code Evaluation (SCA) instruments for vulnerabilities. These strategies lack the organizational-specific context wanted to make an knowledgeable scoring resolution: the rating, even when crucial, won’t really be crucial for a company as a result of its infrastructure works in a singular method – affecting the precise influence the vulnerability might need.
In different phrases, since these instruments depend upon a comparatively naive methodology to find out a vulnerability’s threat, they find yourself with primarily irrelevant vulnerability scores – making figuring out which vulnerabilities to handle first a lot tougher.
Moreover, they don’t handle many provide chain assaults, resembling typosquatting, malicious code injection, CI/CD assaults, and so forth. This oversight misleads Utility Safety (AppSec) groups and builders into specializing in much less crucial points, thus delaying the event course of and leaving the group susceptible to vital assault vectors.
Myrror Safety develops progressive options to those challenges by revolutionizing how organizations detect, prioritize and remediate their provide chain dangers. Myrror’s platform ensures that AppSec and engineering groups sort out the best points on the proper time by using binary-to-source evaluation for each third-party bundle within the codebase. In contrast to conventional SCA instruments that assess influence utilizing version-level detection in manifest recordsdata, Myrror makes use of a proprietary reachability vulnerability evaluation algorithm. This algorithm identifies which vulnerabilities are literally reachable in manufacturing, thus enabling Myrror to prioritize safety points precisely.
This Platform Evaluate will information you thru your entire Myrror person journey, from the preliminary SCM integration to the remediation plan generator, and supply a concise overview of the improvements Myrror Safety has launched to forestall alert fatigue, empower your group to work extra successfully and defend it from the threats of the trendy software program provide chain. To get a personalised demo, go to their web site right here.
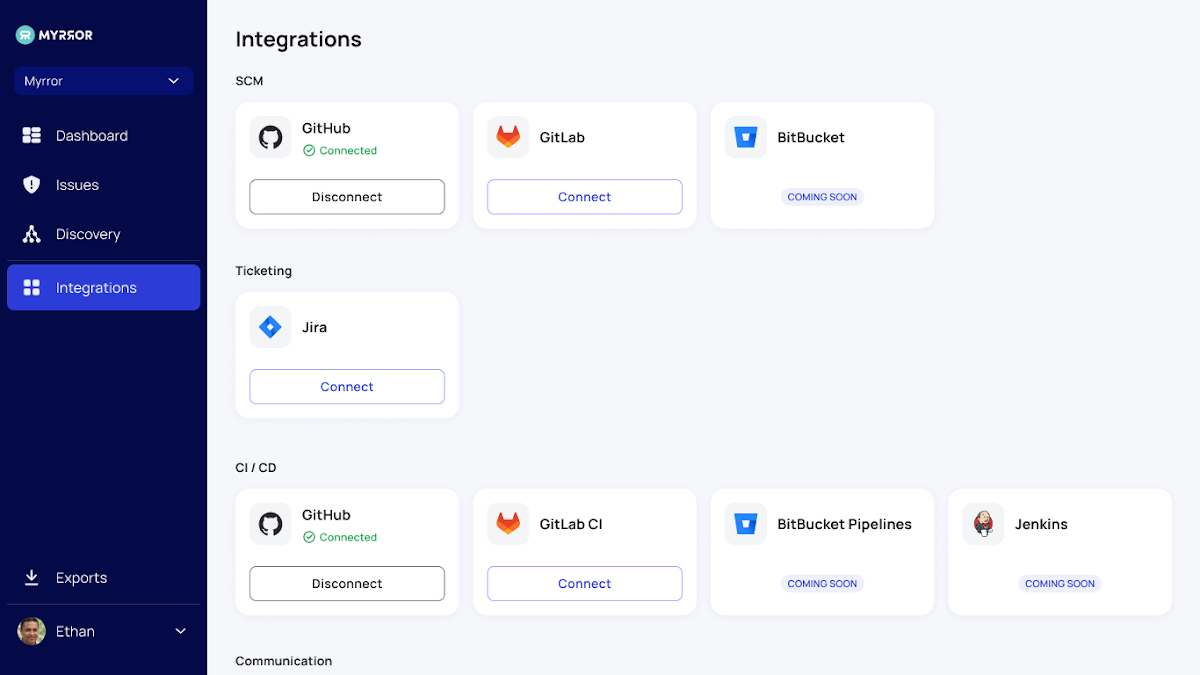
Getting Began and Setup
Myrror is designed for simple set up on the group’s current supply code administration platform. When Myrror is linked to your SCM, a discovery technique of the group’s dependencies begins. The group can later choose particular repositories for lively vulnerability and provide chain assault scanning, offering a prioritized overview of recognized dangers.
The Discovery Part
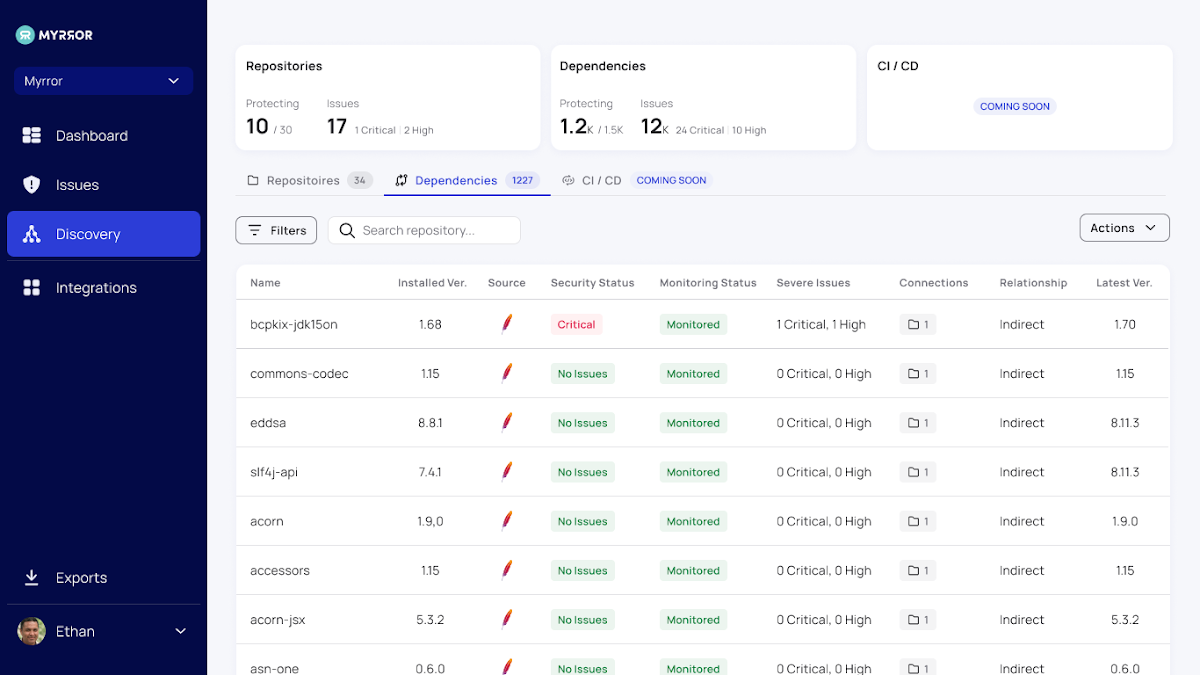
This part allows you to take inventory of the availability chain threat related along with your codebase and decide the precise menace panorama you are uncovered to out of your open-source dependencies.
The Repositories tab exhibits you all the problems in every monitored repository and permits you to select which to watch and which to disregard. This can help you take away some noise related to repositories that aren’t in lively use, will quickly be deprecated, or are merely irrelevant. This tab serves because the management panel over your whole repositories. It enhances the problems display screen by pointing you towards your most at-risk repositories – permitting for a project- or application-level “chicken’s eye” view of the threats.
The Dependencies tab aggregates each open-source dependency in your codebase and creates a graph of all of the repositories by which every one is used. This key overview permits you to get an entire image of the open-source libraries your group depends upon. Regardless of the immense enhance in open-source repositories in mainly each software program venture, organizations have no management over exterior dependencies; taking stock of what’s being utilized in your code is step one to controlling what’s occurring.
The Myrror Dashboard
As soon as the set up is full and the person chooses the repositories to scan, the Myrror dashboard is populated with details about your repositories, their dependencies, and the problems they include. When the person chooses to watch further repositories or join extra SCM sources, the dashboard is robotically up to date with extra details about the brand new codebases.
The dashboard offers high-level insights into the problems throughout your entire set of the group’s codebase, together with:
- Detection Standing
- Points by class
- Dependencies with Safety Standing
- The Riskiest Repository
- Points per code language,
- Standing of Remediation
- Out-of-data Dependencies
- And extra
These charts and graphs generate an in depth and full overview, offering organizations with clear insights into areas requiring probably the most work. Notice the repository filter on the highest proper – this enables particular groups to get correct details about their work and the repositories they’re accountable for and export solely the related knowledge for them.
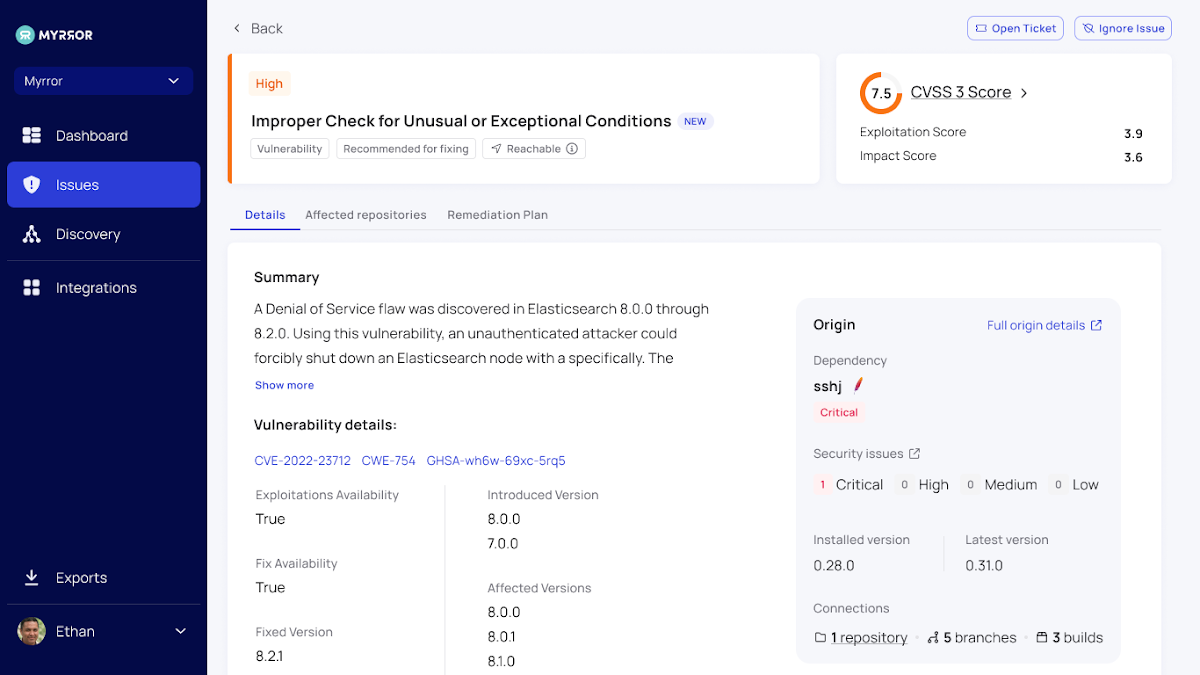
The Points Display screen
That is the core of the Myrror Safety platform. Right here, all of your points are prioritized and flagged in line with their precise severity, reachability, and exploitability for a transparent understanding of what to sort out subsequent. Varied parameters are organized into columns, providing extra profound insights into every particular problem.
Amongst these parameters, the reachability column units Myrror other than conventional SCA platforms. It assesses whether or not the difficulty is definitely reachable in manufacturing, which components into the prioritization – guaranteeing reachable vulnerabilities may be tackled first.
However the platform would not cease at prioritizing vulnerabilities in line with reachability – it additionally considers whether or not it is a direct or oblique dependency, whether or not a repair is offered to remediate the difficulty, and whether or not an exploit has been confirmed to exist within the wild. All of those parameters assist the platform prioritize points precisely and reliably.
You may see all the next items of details about every vulnerability:
- Severity (taking all of the above components under consideration)
- Origin
- Reachability
- Dependency File(s)
- Class – Vulnerability / Provide Chain Assault (see extra within the Detecting Provide Chain Assaults part)
- Exploit Availability
- Repair Availability
- Dependency Relationship
- First Seen
- Authentic Commit
Filters (together with a repository filter) can be found right here too, together with an choice to export the desk and obtain insights for report creation. This assists safety groups in sustaining data in native storage and producing inside audit experiences. These experiences, emailed to the person, include complete data straight from the platform that may be shared with different crew members and stakeholders.
Notice that there are 3 totally different tabs out there on this display screen:
- The “All” tab incorporates all the problems mixed, offering knowledge insights in a single web page concerning the general provide chain menace panorama – together with vulnerabilities and assaults.
- The “really helpful” tab incorporates the precise points really helpful for remediation per severity and reachability – basically your “go-to” pane when deciding what to sort out first.
- Lastly, the “Low Danger” tab has points which you can take care of at a later cut-off date.
Every problem additionally has its in-depth evaluation, with insights on the influence, scope, and origin of the problems proven on one display screen. This detailed overview offers exterior hyperlinks to the CVE to be taught extra about it, in addition to details about the affected repositories and a concrete remediation plan to make sure swift motion may be taken on every problem.
The first tabs out there on this display screen are:
- Particulars – a major overview of the vulnerability or provide chain assault
- Affected Repositories – an inventory of all repositories that depend upon this bundle, permitting you to “join the dots” throughout your entire monitored codebase
- Remediation Plan – Myrror calculates the optimum path of remediation, guaranteeing that the smallest quantity of newly-introduced vulnerabilities find yourself within the codebase after the remediation course of is full
- Assault Overview (see subsequent part for extra particulars)
Detecting Provide Chain Assaults
Remember that Myrror does extra than simply detect vulnerabilities – it additionally detects varied types of provide chain assaults – together with however not restricted to:
- Typosquatting
- Dependency Confusion
- Malicious Code In Repo / Code Injection
- CI/CD Assault
When it detects these assaults, the detection mechanism and remediation plan won’t be as simple as regular vulnerabilities. In these instances, Myrror will present a extra in-depth evaluation of the assault, enabling practitioners to know the state of affairs and pinpoint the concrete hyperlink within the chain that is at fault. See under for an instance of Myrror’s evaluation of a code injection assault:
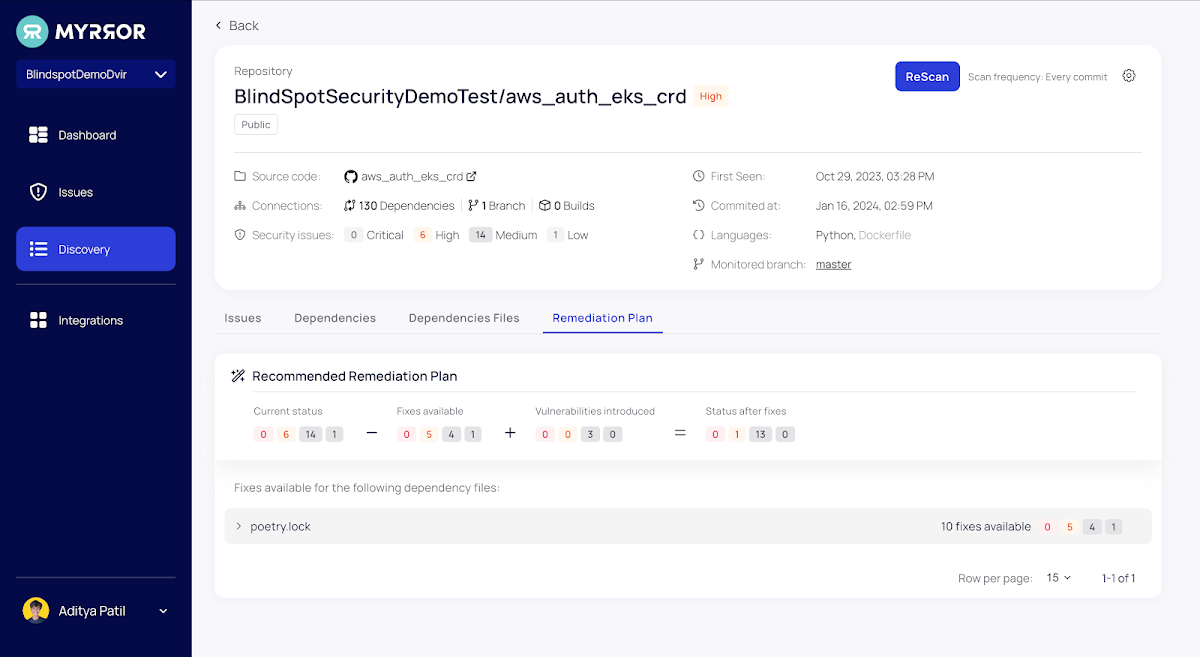
The Remediation Plan Generator
Planning your remediation efforts usually requires comprehending the brand new threats launched throughout patching. Most often, making use of a patch ends in a brand new set of vulnerabilities because of the new dependencies (and their transitive dependencies) it introduces.
For each monitored repository, Myrror simplifies the difficulty remediation course of by robotically calculating the variety of fixes out there for all the problems, what number of new vulnerabilities might be launched in the course of the remediation course of, and what number of points will stay on the finish.
Conclusion
AppSec groups endure from profound alert fatigue in the present day, pushed by an amazing quantity of safety points and a scarcity of clear prioritization of what to work on first. As well as, most groups are utterly unaware of the availability chain assaults they’re uncovered to and don’t have any clear path for detecting them or providing correct remediation.
Myrror’s Reachability-based prioritization affords a method out of vulnerability hell. On the identical time, their binary-to-source evaluation mechanism allows detection of extra than simply easy vulnerabilities – and permits you to defend in opposition to a bunch of provide chain assaults.
You may e book a demo to be taught extra on their web site right here.