A novel malware marketing campaign has been noticed focusing on Redis servers for preliminary entry with the final word objective of mining cryptocurrency on compromised Linux hosts.
“This explicit marketing campaign includes the usage of various novel system weakening strategies towards the information retailer itself,” Cado safety researcher Matt Muir mentioned in a technical report.
The cryptojacking assault is facilitated by a malware codenamed Migo, a Golang ELF binary that comes fitted with compile-time obfuscation and the power to persist on Linux machines.
The cloud safety firm mentioned it detected the marketing campaign after it recognized an “uncommon sequence of instructions” focusing on its Redis honeypots which are engineered to decrease safety defenses by disabling the next configuration choices –
It is suspected that these choices are turned off as a way to ship further instructions to the Redis server from exterior networks and facilitate future exploitation with out attracting a lot consideration.
This step is then adopted by menace actors organising two Redis keys, one pointing to an attacker-controlled SSH key and the opposite to a cron job that retrieves the malicious major payload from a file switch service named Switch.sh, a way beforehand noticed in early 2023.
The shell script to fetch Migo utilizing Switch.sh is embedded inside a Pastebin file that is, in flip, obtained utilizing a curl or wget command.
 |
| Persistence |
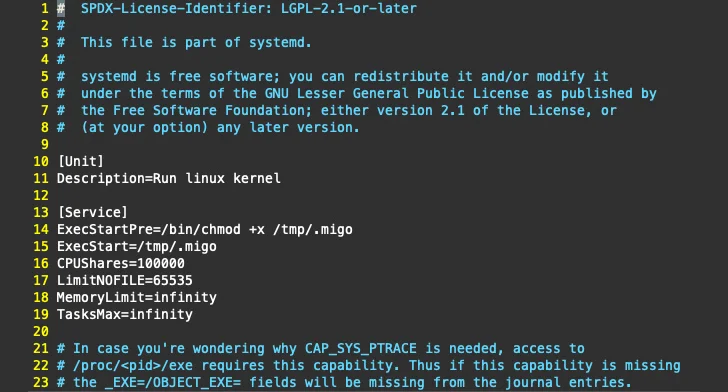
The Go-based ELF binary, moreover incorporating mechanisms to withstand reverse engineering, acts as a downloader for an XMRig installer hosted on GitHub. It is also accountable for performing a sequence of steps to ascertain persistence, terminate competing miners, and launch the miner.
On high of that, Migo disables Safety-Enhanced Linux (SELinux) and searches for uninstallation scripts for monitoring brokers bundled in compute cases from cloud suppliers resembling Qcloud and Alibaba Cloud. It additional deploys a modified model (“libsystemd.so”) of a well-liked user-mode rootkit named libprocesshider to cover processes and on-disk artifacts.
It is value mentioning that these actions overlap with techniques adopted by recognized cryptojacking teams like TeamTNT, WatchDog, Rocke, and menace actors related to the SkidMap malware.
“Curiously, Migo seems to recursively iterate via information and directories beneath /and many others,” Muir famous. “The malware will merely learn information in these places and never do something with the contents.”
“One concept is that this might be a (weak) try to confuse sandbox and dynamic evaluation options by performing a lot of benign actions, leading to a non-malicious classification.”
One other speculation is that the malware is searching for an artifact that is particular to a goal atmosphere, though Cado mentioned it discovered no proof to help this line of reasoning.
“Migo demonstrates that cloud-focused attackers are persevering with to refine their strategies and enhance their skill to use web-facing companies,” Muir mentioned.
“Though libprocesshider is incessantly utilized by cryptojacking campaigns, this explicit variant contains the power to cover on-disk artifacts along with the malicious processes themselves.”