You hear quite a bit about zero belief microsegmentation as of late and rightly so. It has matured right into a confirmed safety best-practice to successfully stop unauthorized lateral motion throughout community sources. It entails dividing your community into remoted segments, or “microsegments,” the place every phase has its personal set of safety insurance policies and controls. On this approach, even when a breach happens or a possible risk good points entry to a useful resource, the blast radius is contained.
And like many safety practices, there are alternative ways to attain the target, and usually a lot of it is determined by the distinctive buyer surroundings. For microsegmentation, the secret’s to have a trusted accomplice that not solely offers a strong safety resolution however provides you the pliability to adapt to your wants as an alternative of forcing a “one dimension matches all” strategy.
Now, there are broadly two totally different approaches you’ll be able to take to attain your microsegmentation goals:
- A number-based enforcement strategy the place the insurance policies are enforced on the workload itself. This may be completed by putting in an agent on the workload or by leveraging APIs in public cloud.
- A network-based enforcement strategy the place the insurance policies are enforced on a community machine like an east-west community firewall or a change.
Whereas a host-based enforcement strategy is immensely highly effective as a result of it offers entry to wealthy telemetry when it comes to processes, packages, and CVEs operating on the workloads, it could not at all times be a practical strategy for a myriad of causes. These causes can vary from software group perceptions, community safety group preferences, or just the necessity for a unique strategy to attain buy-in throughout the group.
Lengthy story brief, to make microsegmentation sensible and achievable, it’s clear {that a} dynamic duo of host and network-based safety is vital to a strong and resilient zero belief cybersecurity technique. Earlier this 12 months, Cisco accomplished the native integration between Cisco Safe Workload and Cisco Safe Firewall delivering on this precept and offering prospects with unmatched flexibility in addition to protection in depth. Let’s take a deeper have a look at what this integration permits our prospects to attain and a number of the use instances.
Use case #1: Community visibility through an east-west community firewall
The journey to microsegmentation begins with visibility. It is a good alternative for me to insert the cliché right here – “What you’ll be able to’t see, you’ll be able to’t defend.” Within the context of microsegmentation, circulate visibility offers the muse for constructing a blueprint of how purposes talk with one another, in addition to customers and gadgets – each inside and outdoors the datacenter.
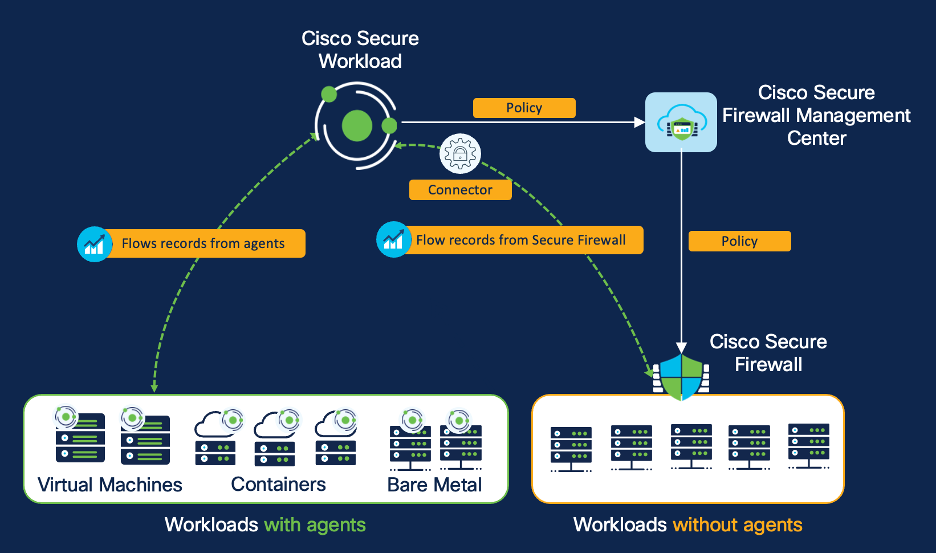
The combination between Safe Workload and Safe Firewall permits the ingestion of NSEL circulate data to supply community circulate visibility, as proven in Determine 1. You’ll be able to additional enrich this community circulate knowledge by bringing in context within the type of labels and tags from exterior techniques like CMDB, IPAM, identification sources, and many others. This contextually enriched knowledge set permits you to rapidly determine the communication patterns and any indicators of compromise throughout your software panorama, enabling you to right away enhance your safety posture.
Determine 1: Safe Workload ingests NSEL circulate data from Safe Firewall

Use case #2: Microsegmentation utilizing the east-west community firewall
The combination of Safe Firewall and Safe Workload offers two highly effective complimentary strategies to find, compile, and implement zero belief microsegmentation insurance policies. The power to make use of a host-based, network-based, or mixture of the 2 strategies provides you the pliability to deploy within the method that most closely fits your small business wants and group roles (Determine 2).
And whatever the strategy or combine, the combination allows you to seamlessly leverage the complete capabilities of Safe Workload together with:
- Coverage discovery and evaluation: Mechanically uncover insurance policies which are tailor-made to your surroundings by analyzing circulate knowledge ingested from the Safe Firewall defending east-west workload communications.
- Coverage enforcement: Onboard a number of east-west firewalls to automate and implement microsegmentation insurance policies on a selected firewall or set of firewalls by way of Safe Workload. (For extra on this functionality, Topology Consciousness, learn my colleague’s weblog Topology Issues).
- Coverage compliance monitoring: The community circulate info, when put next in opposition to a baseline coverage, offers a deep view into how your purposes are behaving and complying in opposition to insurance policies over time.
Determine 2: Host-based and network-based strategy with Safe Workload
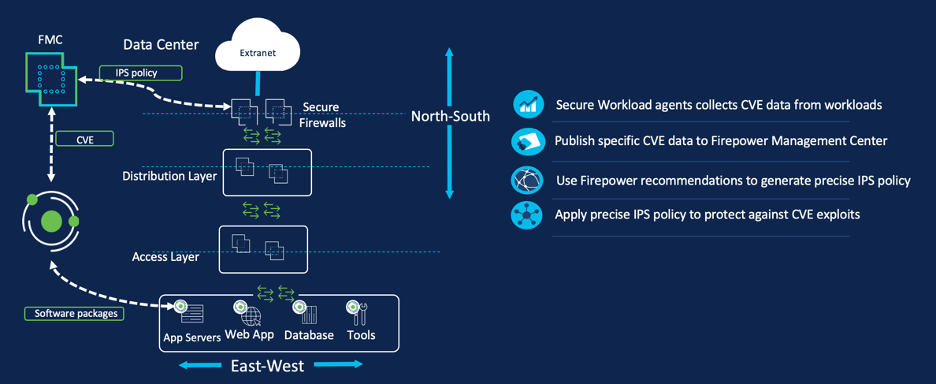
Use case #3: Protection in depth with digital patching through north-south community firewall
This use case demonstrates how the combination delivers protection in depth and in the end higher safety outcomes. In immediately’s quickly evolving digital panorama, purposes play a significant position in each side of our lives. Nonetheless, with the elevated reliance on software program, cyber threats have additionally turn out to be extra refined and pervasive. Conventional patching strategies, though efficient, could not at all times be possible resulting from operational constraints and the chance of downtime. When a zero-day vulnerability is found, there are a number of totally different situations that play out. Think about two frequent situations: 1) A newly found CVE poses an instantaneous threat and on this case the repair or the patch shouldn’t be accessible and a pair of) The CVE shouldn’t be extremely vital so it’s not price patching it exterior the same old patch window due to the manufacturing or enterprise affect. In each instances, one should settle for the interim threat and both await the patch to be accessible or for the patch window schedule.
Digital patching, a type of compensating management, is a safety follow that permits you to mitigate this threat by making use of an interim safety or a “digital” repair to recognized vulnerabilities within the software program till it has been patched or up to date. Digital patching is often completed by leveraging the Intrusion Prevention System (IPS) of Cisco Safe Firewall. The important thing functionality, fostered by the seamless integration, is Safe Workload’s capacity to share CVE info with Safe Firewall, thereby activating the related IPS insurance policies for these CVEs. Let’s check out how (Determine 3):
- The Safe Workload brokers put in on the appliance workloads will collect telemetry concerning the software program packages and CVEs current on the appliance workloads.
- A workload-CVE mapping knowledge is then printed to Safe Firewall Administration Middle. You’ll be able to select the precise set of CVEs you wish to publish. For instance, you’ll be able to select to solely publish CVEs which are exploitable over community as an assault vector and has CVSS rating of 10. This might will let you management any potential efficiency affect in your IPS.
- Lastly, the Safe Firewall Administration Middle then runs the ‘firepower suggestions’ device to positive tune and allow the precise set of signatures which are wanted to supply safety in opposition to the CVEs that had been discovered in your workloads. As soon as the brand new signature set is crafted, it may be deployed to the north-south perimeter Safe Firewall.
Determine 3: Digital patching with Safe Workload and Safe Firewall
Flexibility and protection in depth is the important thing to a resilient zero belief microsegmentation technique
With Safe Workload and Safe Firewall, you’ll be able to obtain a zero-trust safety mannequin by combining a host-based and network-based enforcement strategy. As well as, with the digital patching capacity, you get one other layer of protection that permits you to keep the integrity and availability of your purposes with out sacrificing safety. Because the cyber risk panorama continues to evolve, concord between totally different safety options is undoubtedly the important thing to delivering simpler options that defend priceless digital property.
Be taught extra about Cisco Safe Workload and Cisco Safe Firewall
Join a Safe Workload workshop
We’d love to listen to what you suppose. Ask a Query, Remark Under, and Keep Related with Cisco Safety on social!
Cisco Safety Social Channels
Share:















