Lenovo, AMI and Insyde have launched patches for LogoFAIL, a picture library poisoning assault.
Researchers at firmware provide chain safety platform firm Binarly found a set of safety vulnerabilities that open virtually all Home windows and Linux computer systems as much as assault. The safety researchers named the assault LogoFAIL due to its origins in picture parsing libraries. Binarly introduced its discovery on Nov. 29 and held a coordinated mass disclosure on the Black Hat Safety Convention in London on Dec. 6.
Any x86 or ARM-based system utilizing the Unified Extensible Firmware Interfaces firmware ecosystem may probably be open to the LogoFAIL assault. Binarly continues to be investigating whether or not further producers are affected. LogoFAIL is especially harmful as a result of it may be remotely executed in methods many endpoint safety merchandise can’t detect.
This vulnerability just isn’t identified to have been exploited, although a number of distributors have launched patches.
Soar to:
How does the LogoFAIL assault work?
LogoFAIL is a sequence of vulnerabilities whereby the graphic picture parsers in system firmware can use custom-made variations of picture parsing libraries. Primarily, an attacker can substitute a picture or emblem (thus the identify) that seems whereas the system boots up and acquire entry to the working system and reminiscence from there (Determine A).
Determine A
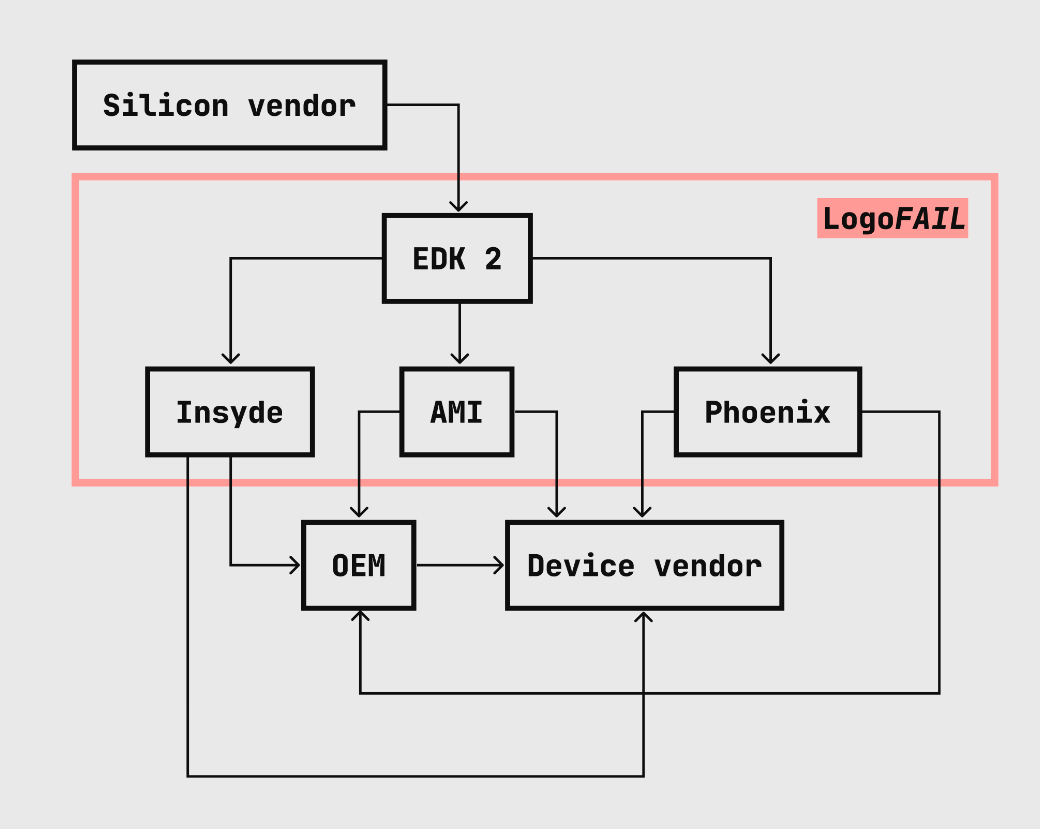
Assaults based mostly on the UEFI system firmware have been round for the reason that early 2000s, however “… the variety of picture parsers have considerably elevated through the years,” Binarly wrote. Extra picture parsers means a wider assault floor.
Put merely, attackers may embed malicious code into logos that seem through the Driver Execution Surroundings stage within the boot course of, such because the system producer’s emblem. From there, attackers can entry and management the system’s reminiscence and disk (Determine B). Binarly has a technical rationalization.
Determine B
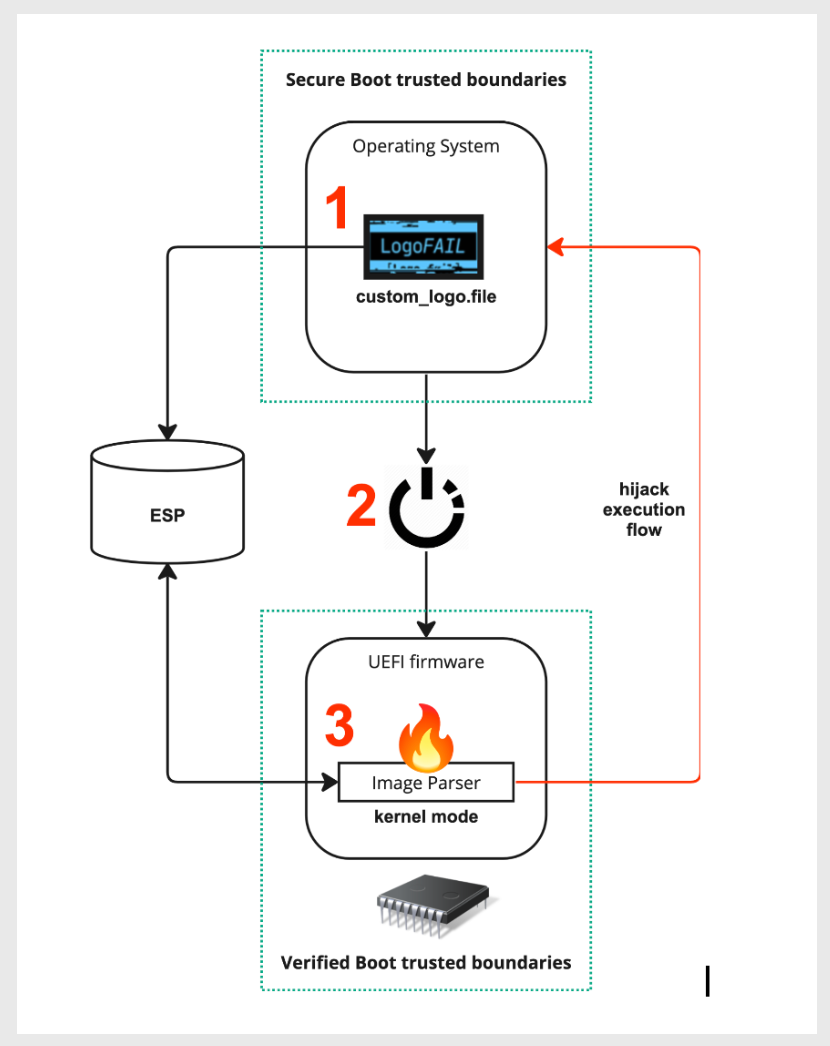
Binarly confirmed they might load executable code onto the arduous drive earlier than the system had absolutely booted up.
“Now we have been closely centered on reporting vulnerabilities primarily found by the Binarly Transparency Platform product, however the work on LogoFAIL was totally different and initially initiated as a small analysis challenge only for enjoyable,” Binarly’s staff wrote. “After demonstrating an enormous variety of attention-grabbing assault surfaces from image-parsing firmware parts, the challenge grew into an enormous industry-wide disclosure.”
SEE: Cisco Talos analyzed cybersecurity traits of 2023 (TechRepublic)
defend in opposition to LogoFAIL
The next corporations have launched patches for LogoFAIL:
ArsTechnica recommends working UEFI defenses akin to Safe Boot, Intel Boot Guard, Intel BIOS Guard or their equivalents for AMD or ARM CPUs. Tech division leaders ought to inform staff how one can obtain patches as acceptable.